- What are Endpoint Security Management Challenges?
- What Is the Impact of Endpoint Security on System Performance?
- What are the Requirements for Securing Endpoints?
- What is the Role of AI in Endpoint Security?
- 3 Ways to Prevent Evasive Threats
- Why Endpoints Shouldn't Rely Entirely On Scanning?
- How Do I Measure Endpoint Security Effectiveness?
-
What Is Endpoint Scanning?
- Endpoint Scanning Explained
- Why Endpoint Scanning Is Crucial for Modern Cybersecurity
- How Endpoint Scanning Works: A Multi-Faceted Process
- Types of Endpoint Scans
- Key Steps for Effective Endpoint Scanning
- Challenges and Limitations in Endpoint Scanning
- Enhancing Endpoint Scanning with Advanced Technologies
- Best Practices for Optimizing Endpoint Scanning
- Endpoint Scanning vs. Other Endpoint Security Solutions
- Future Trends in Endpoint Scanning
- Endpoint Scanning FAQs
-
Extending Zero Trust To The Endpoint
- 5 Ways Endpoint Security and Network Security Work Together
What Is Endpoint Protection for Enterprises?
Endpoint protection is a comprehensive system of tools, services, and processes designed to protect endpoints against the full range of endpoint threats, such as malware, ransomware, and Zero Day threats. Those endpoints span traditional computer products such as notebooks, desktops, and servers to Internet of Things (IoT) devices, digital signage, wearable computers, and vehicle-mounted computers. Endpoint protection is a core tenet of enterprise-wide endpoint security.

Figure 1: Endpoint security integrations provide comprehensive protection for digital endpoints.
Why Endpoint Protection Is Essential
There are several reasons why endpoint protection is so valuable as part of any organization's enterprise-wide security.
First, the massive growth in the number and diversity of endpoints has made endpoint protection more challenging and complex. With those challenges and complexities come increased risk and difficulty for security teams working in a Security Operations Center (SOC), at an organization's remote offices, or as part of an organization's network of third-party security service providers.
Delve into the various endpoints and learn why they are vulnerable to attacks by cyber criminals: What Is an Endpoint?
Second, hackers are known to target endpoints as their primary attack vector when looking to exfiltrate data, break into an organization's network, or to lock up essential files in a ransomware attempt. Protecting an endpoint therefore is a top priority for protecting an organization's digital assets, including identities and credentials.
Third, the increased trend toward remote work or hybrid work means that many employees are working at least occasionally from home or another location other than a traditional headquarters facility. In many cases, those employees' computers, smartphones, tablets, applications, and cloud services are only sometimes using the most up-to-date and strongest security solutions to protect their endpoints, such as threat detection software.
How Endpoint Protection Operates
Endpoint protection platforms and other solutions require several necessary steps. These include reacting to threats, detection, response, proactive steps, and management/reporting.
Antivirus, anti-malware software, and firewall protection (especially next-generation firewalls with more sophisticated preventative functionality) are preventative measures for endpoint protection.
Detection and response are often deployed as part of an Endpoint Detection and Response (EDR) toolset or services. These use continuous monitoring to spot various threats and collect essential data about endpoint activity. They then send automated alerts to security teams and incident response teams.
Proactive security measures include capabilities such as device control, access control, and application control.
Finally, centralized management is a key part of endpoint protection because it allows security administrators to monitor endpoint activity, investigate incidents, and configure/manage policies.
The Evolution of Endpoint Protection
1980s: Antivirus
Endpoint security has evolved beyond the basic capabilities provided by antivirus tools back in the 1980s, which scanned endpoint files for malware.
2000s: Next-Generation Antivirus (NGAV)
To combat new forms of malware, machine learning and behavioral threat protection was introduced to create more effective next-gen antivirus in the early 2000s.
2010s: Endpoint Protection Platform (EPP)
Endpoint protection platforms, or EPPs, combine antivirus or next-gen antivirus, personal firewall, encryption, USB device control, vulnerability assessment and more to deliver a complete platform to stop malware from penetrating endpoints.
2015: Endpoint Detection and Response (EDR)
Gartner Analyst Anton Chuvakin coined the term "endpoint threat detection and response" to describe "the tools primarily focused on detecting and investigating suspicious activities" on endpoints in 2013. This name had evolved to endpoint detection and response by 2015.
2021: Extended Detection and Response (XDR)
While the concept of XDR was first introduced in 2019 by Palo Alto Networks, XDR is considered an emerging technology that is quickly gaining traction in the endpoint security market.
While most technology providers now offer endpoint security offerings that combine EPP/EDR capabilities, only some offer a true XDR solution that combines many data sources into one platform for analysis and remediation.
Explore endpoint security to learn how it protects networks from threats and adapts to modern digital challenges: What Is Endpoint Security?
Defining Endpoint Protection Platform
Industry research leader Gartner defines an EPP as "a solution deployed on endpoint devices to prevent file-based malware attacks, detect malicious activity, and provide the investigation and remediation capabilities needed to respond to dynamic security incidents and alerts."
"Detection capabilities will vary, but advanced solutions will use multiple detection techniques, ranging from static IOCs to behavioral analysis. Desirable EPP solutions are primarily cloud-managed, allowing the continuous monitoring and collection of activity data and the ability to take remote remediation actions, whether the endpoint is on the corporate network or outside of the office."
How Endpoint Protection Differs From Endpoint Detection and Response (EDR)
"Endpoint protection" typically refers to the full spectrum of tools, processes, and services utilized to protect an organization's full array of endpoints, regardless of location or format. It can be considered a strategic approach to endpoint security, encompassing a number of different tools and services. One of those toolsets is Endpoint Detection and Response (EDR), a vital part of an overall endpoint protection framework.
An EDR solution uses capabilities such as continuous monitoring, integrated threat intelligence, firewalls, access control, and more to proactively scan endpoint data for activity that might indicate a potential attack or compromise that could result in a security incident, such as a malware infection or a data breach. EDR tools are an invaluable part of a broader endpoint protection strategy.
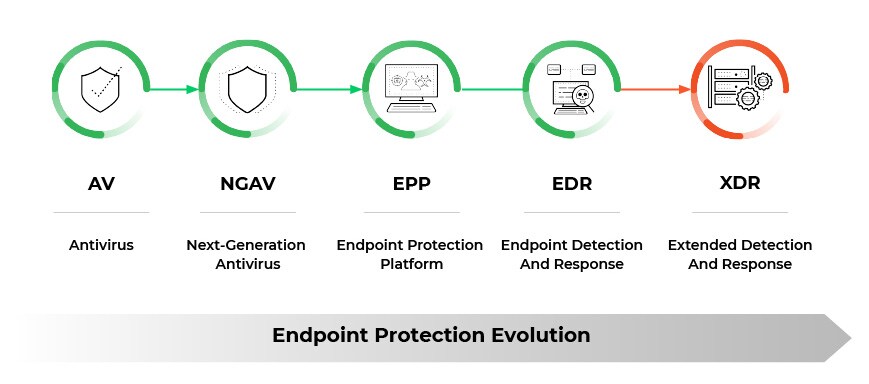
Figure 2: The Evolution of Endpoint Protection
Threats Endpoint Protection Defends Against
Endpoint protection bolsters an organization's defenses against a large and growing number of threats, vulnerabilities, and attack vectors. Among the most prevalent and commonly occurring endpoint threats are malware, advanced persistent threats, phishing, and social engineering.
Other types of endpoint attacks that an endpoint protection strategy must identify and defeat include:
- Credentials theft
- Unauthorized network access
- Fileless malware
- Ransomware
- Data leakage
Finally, one more important risk to strong endpoint security is insider threats, which may be negligent or malicious. Inadvertent, accidental endpoint attacks come from improper security control configurations or simple user errors that may result in an "open door" for hackers.
Malicious insiders, however, are extremely dangerous because they have the access, the means, and the opportunity to gain access to data they may choose to exfiltrate or send to third parties. Organizations must have an incident response plan and appropriate response capabilities to prevent any detected threat from spreading throughout the network and related systems.
Explore how endpoint antivirus solutions have evolved to incorporate more sophisticated techniques like behavior-based and heuristic analysis: What Is Endpoint Security Antivirus?
Components of Endpoint Protection

Endpoint protection consists of multiple security components that work together to safeguard devices from cyber threats. An endpoint protection platform (EPP) is a solution deployed on endpoint devices to prevent file-based malware attacks, detect malicious activity, and provide the investigation and remediation capabilities needed to respond to dynamic security incidents and alerts.
Prevention Components
Next-Generation Antivirus (NGAV): Advanced EPP solutions use multiple detection techniques including artificial intelligence (AI), behavioral analysis, threat intelligence and human threat hunters. Goes beyond traditional signature-based detection to identify unknown malware and zero-day threats.
Anti-Malware Engines: Antivirus and antimalware programs remain pivotal in endpoint security, constantly safeguarding against an extensive range of malicious software. Designed to detect, block, and eliminate threats, they utilize techniques such as signature-based scanning, heuristic analysis, and behavioral assessment.
Application Control: Manages and restricts which applications can execute on endpoints, preventing unauthorized software installation and execution while maintaining legitimate business functionality.
Device Control: Controls access to USB ports, external storage devices, optical drives, and other peripheral connections to prevent data theft and malware introduction through removable media.
Host-Based Firewall: Provides network-level protection directly on the endpoint, filtering inbound and outbound network traffic based on predefined security rules and policies.
Detection Components
Behavioral Analysis: Monitors system processes, file activities, and network communications to identify suspicious behaviors that may indicate compromise, even when specific malware signatures are unknown.
Sandboxing: Sandboxing isolates potentially harmful software within a designated controlled environment, safeguarding the broader system from possible threats. This isolation prevents any negative impact that the software might have if it were malicious.
Threat Intelligence Integration: Real-time feeds providing current information about emerging threats, malicious indicators of compromise (IoCs), and attack patterns to enhance detection capabilities.
Intrusion Detection and Prevention: Monitors network traffic and system activities for signs of malicious activity or policy violations, with capabilities to automatically block detected threats.
Data Protection Components
Data Loss Prevention (DLP): Data loss prevention (DLP) solutions can provide visibility into data flows and help to block attempted exfiltration of sensitive information.
Data Encryption: Protects sensitive data both at rest and in transit, ensuring that even if devices are compromised or stolen, the data remains inaccessible to unauthorized parties.
Ransomware Protection: Specialized detection mechanisms that identify encryption-based attacks and can automatically create backup copies or restore encrypted files.
Response and Management Components
Centralized Management Console: Cloud-managed solutions allowing continuous monitoring and collection of activity data, along with the ability to take remote remediation actions, whether the endpoint is on the corporate network or outside of the office.
Automated Response Capabilities: Immediate containment actions including network isolation, process termination, file quarantine, and system remediation to minimize threat impact.
Forensics and Investigation Tools: Detailed logging, timeline analysis, and evidence collection capabilities for incident investigation and compliance reporting.
Update and Intelligence Components
Cloud-Based Intelligence: Cloud-data-assisted capabilities where the endpoint agent does not have to maintain a local database of all known IOCs, but can check a cloud resource to find the latest verdicts on objects that it is unable to classify.
Automatic Updates: Real-time delivery of security updates, threat definitions, and policy changes without requiring manual intervention from administrators.
These components integrate to provide comprehensive endpoint protection, with each element addressing specific attack vectors while contributing to an overall defense-in-depth security strategy.
Explore key strategies to safeguard systems effectively in our comprehensive guide: What Is an Endpoint Security Solution?
Finally, endpoint protection usually includes one of the major forms of detection and response tools and services. These include:
- EDR (Endpoint Detection and Response) continually monitors data movement on endpoints and aligns with threat intelligence services to identify potential threats, block them, and, if necessary, remediate their impact.
- Managed Detection and Response (MDR) is similar to EDR but managed by an outsourced, third-party organization that reports to the organization's security operations team.
- Extended Detection and Response (XDR), which protects all parts of an organization's digital infrastructure, not just endpoints. XDR may be deployed and managed either as an in-house solution or as an outsourced service.
Endpoint Protection Use Cases
Endpoint protection is broadly applicable to organizations of all sizes, in all industries, with different degrees of technical sophistication, and across all geographic regions. There are numerous use cases for deploying endpoint protection solutions because endpoint systems' growing prevalence and importance are continuing unabated.
In fact, with the increased adoption of Internet of Things technology, it's clear that the sheer number of endpoints will skyrocket in the coming years. There are many important use cases where organizations should deploy endpoint protection solutions. These include:
- Malware Prevention: Endpoint protection solutions employ signature-based detection, heuristic analysis, and behavioral monitoring to prevent endpoint malware infections.
- Device Control: Device control features to manage and restrict the use of peripheral devices, such as USB drives and external storage devices.
- Application Control: Organizations must define and enforce policies governing applications that run on endpoints.
- Endpoint Detection and Response (EDR): Real-time monitoring and response capabilities are vital to detect and respond to advanced endpoint threats.
- File and Disk Encryption: Endpoint protection solutions may offer encryption features to encrypt files and disks on endpoints.
- Data Loss Prevention (DLP): DLP features monitor and control the transfer of sensitive data from endpoints and prevent attempts to exfiltrate, steal, or transfer data to unauthorized third parties.
- User Entity Behavior Analytics (UEBA): UEBA features analyze user behavior on endpoints to detect anomalies and potential indicators of compromise.
- Phishing and Social Engineering Protection: Organizations need solutions to detect and block phishing emails, malicious websites, and other social engineering attacks that attempt to trick users.
- Patch Management: These capabilities ensure that endpoints are promptly updated with the latest security patches and software updates.
- Remote Management and Monitoring: Endpoint protection solutions typically include centralized management consoles that allow administrators to remotely deploy, configure, monitor, and manage security policies and updates across all endpoints in the organization.
What to Look for in an Endpoint Protection Platform
Organizations researching and evaluating EPP solutions should consider both the capabilities of the technology solution (the platform) and the skills and experiences of the technology partner providing and supporting the platform.
Deep dive into the core security capabilities that an effective endpoint protection solution should deliver: How Do I Measure Endpoint Security Effectiveness?
From a technology platform perspective, organizations should look for such capabilities as:
- Malware protection powered by machine learning algorithms.
- Demonstrated high scores for MITRE ATT&CK protection and detection.
- Cloud-delivered agents that are deployed in just minutes.
- Integrated next-generation firewall protection.
- Vulnerability assessments.
- AI-driven local analysis at the file level to correctly find and block malware.
- Deployed as a fully integrated endpoint protection suite.
- Simple cloud management to control all endpoints without setting up on-premises log servers and management systems.
- Rapid incident response in the form of forensics-driven investigation and response.