Cloud Identity Security Explained
Cloud identity security represents the evolution of traditional identity and access management (IAM) for the era of distributed infrastructure. Recent threat intelligence shows that identity-driven techniques now account for 65% of initial access incidents.
In legacy on-premises environments, the network perimeter acted as a physical barrier. As organizations migrate to public, private, and hybrid clouds, the traditional boundary has dissolved. Identity now functions as the "master key" for accessing sensitive data, infrastructure, and applications, even when they are spread across various, fragmented environments.
Effective cloud identity security requires a unified approach to managing a diverse set of entities. This includes employees, temporary contractors, customer accounts, and an ever-expanding population of machine identities such as serverless functions, containers, and automated agents. The complexity of these environments often leads to "governance drift," where permissions accumulate over time, leaving 99% of cloud roles over-privileged.
The importance of this discipline is underscored by the fact that attackers no longer need to "break in" via complex exploits; they simply "log in" using stolen credentials or hijacked session tokens. By centralizing identity governance and enforcing strict authentication protocols, organizations can disrupt the attack lifecycle and regain control over their digital footprint.
Why Cloud Identity Security Matters Now
Cloud environments move fast. Teams innovate rapidly. Infrastructure changes hourly. New roles, tokens, workloads, service accounts, and automations are constantly being created. That velocity is great for the business but challenging for security, because permissions are often temporarily broadened and then forgotten.
Unit 42 incident response reporting has repeatedly highlighted identity as a primary entry point, and a major factor across investigations, reinforcing that identity security is now a top control point for reducing breach likelihood and limiting lateral movement.
Use Cases & Real-World Examples
The Palo Alto Networks Unit 42 Global Incident Response Report 2026 highlights that identity loopholes drive nearly 90% of all cyber investigations.
AI-Accelerated Intrusions
Threat actors now use AI to automate reconnaissance and credential stuffing. Unit 42 research shows that the fastest 25% of intrusions reach data exfiltration in just 72 minutes. Organizations without automated identity security cannot respond fast enough to stop these high-velocity attacks.
Privilege Escalation
In cloud environments, misconfigured permissions often allow attackers to move laterally. Unit 42 found that 76% of organizations do not enforce MFA for console users. This lack of control allows a low-level compromise to escalate into a full-scale cloud takeover.
Core Components of a Strong Cloud Identity Framework
A resilient security posture requires a multi-layered approach that addresses the unique complexities of cloud-native infrastructure.
Identity and Access Management (IAM) Foundation
IAM serves as the fundamental system for defining who can access which resources and under what specific conditions. It manages the entire lifecycle of an identity, from initial provisioning and role assignment to the eventual deactivation of accounts.
Multi-Factor Authentication (MFA) and Phishing Resistance
MFA provides a critical layer of defense by requiring multiple independent credentials for verification. Security leaders are now prioritizing phishing-resistant MFA, such as FIDO2-compliant hardware keys, to counter sophisticated adversary-in-the-middle attacks that bypass traditional SMS or push-based codes.
Identity Threat Detection and Response (ITDR)
ITDR focuses specifically on protecting identity infrastructure from active exploitation. This discipline uses behavioral analytics to identify anomalies, such as impossible travel or unusual privilege escalation, enabling security teams to intercept compromised credentials in real time.
How Cloud Identity Security Works
At a high level, cloud identity security answers three questions continuously:
- Who/what is this?M (identity assurance)
- What should it be allowed to do? (authorization and entitlements)
- Is the access safe right now? (context, behavior, risk, and time)
This means implementing controls like the following:
What are Common Governance Challenges?
Most cloud identity security failures aren’t due to missing tools; they happen because visibility and consistency break down as environments scale. When teams can’t clearly see “who has access to what,” permissions become a liability.
- Identity sprawl: Human and machine identities multiply rapidly.
- Entitlement creep: “Temporary” access becomes permanent.
- Inconsistent IAM models across clouds: Policies and roles don’t translate cleanly between providers.
- Standing privileged access: Persistent admin roles and long-lived secrets increase exposure.
- Limited detection for identity abuse: Many orgs monitor endpoints and networks well, but miss identity-layer signals.
Benefits of Cloud Identity Security
When cloud identity security is implemented effectively, it reduces risk without slowing the business. The goal isn’t to make access painful; it’s to make access controlled, observable, and reversible.
- Reduced breach likelihood: Fewer exploitable permissions and less persistent privilege.
- Lower blast radius: Compromised identities have limited reach and duration.
- Faster audits and compliance: Clearer access reporting and controls.
- Better operational consistency: Standardized access governance across cloud services.
- Frictionless user experience in cloud-native tools: Developers and platform engineers innovate quickly without compromising security.
Best Practices for Hardening Cloud Identity
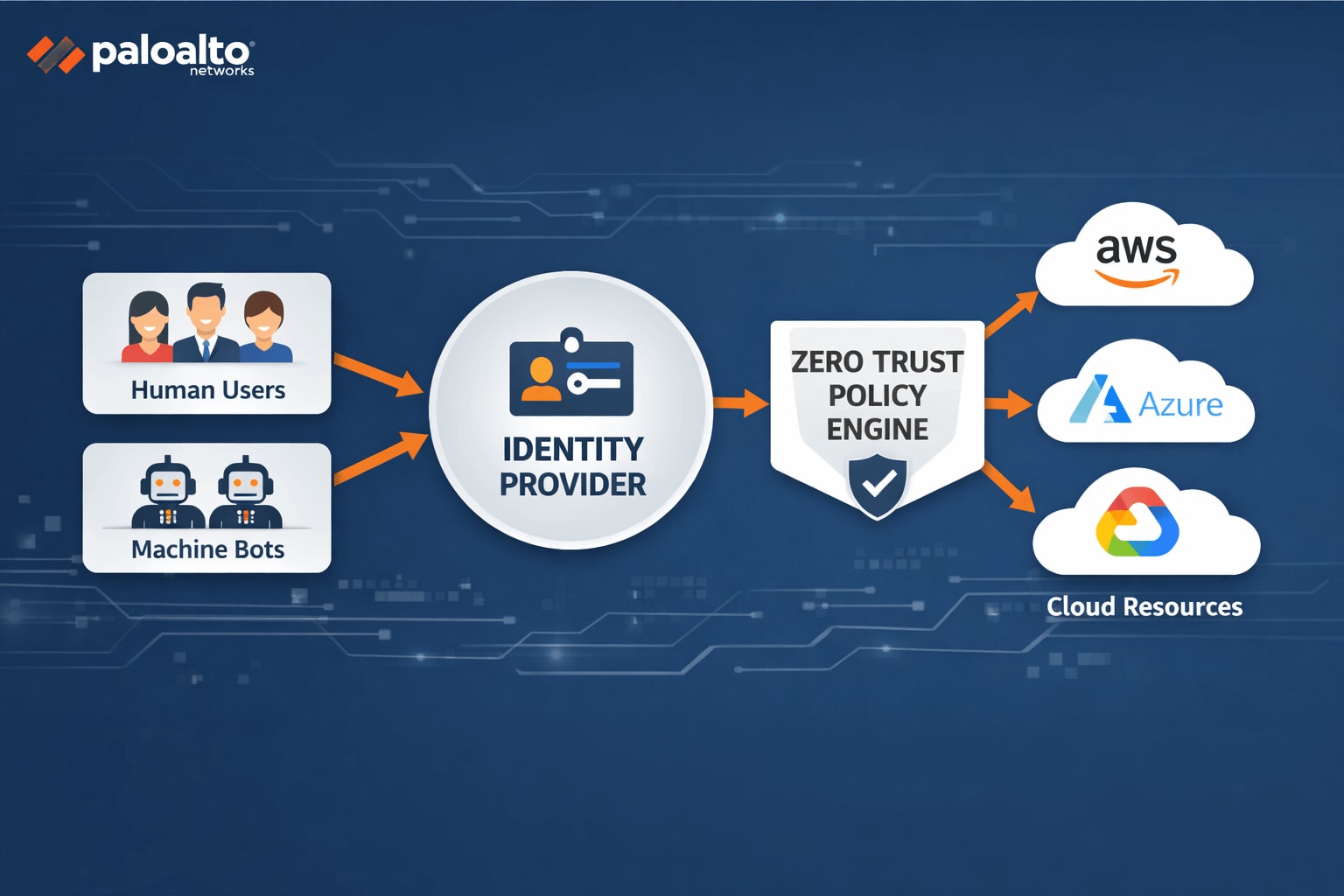
Implementing effective security requires a shift toward a zero trust model. Strengthening identity security requires a combination of strict policy enforcement and automated governance. The following table outlines critical implementation steps for modern enterprises.
How Cloud Identity Security Supports Zero Trust
Zero trust works when access is continuously evaluated, rather than granted once and trusted forever. In the cloud, identity is one of the most important control points for implementing zero trust because it sits directly on the access path to critical resources.
Cloud identity security supports zero trust by enforcing least privilege, reducing standing access, validating access context, and detecting identity misuse early, before the attacker can turn a single credential into full control of the environment.
Cloud Identity Security FAQs