- What Is Access Management?
- What Is Access Control?
- What Is the Principle of Least Privilege?
-
What Is an Application Gateway? Layer 7 Balancing Explained
- App Gateway Explained: Beyond Basic Load Balancing
- The Anatomy of a Request: Listener to Backend Pool
- Key Benefits and Strategic Advantages
- Application Gateway vs. Traditional Tools
- Why Gateways Support Zero Trust
- Implementation Challenges and Solutions
- Advanced Proactive Defense
- Application Gateway FAQs
-
What Is User Behavior Analytics (UBA)?
- User Behavior Analytics Explained
- How UBA Works: The Data-to-Insight Flow
- Core UBA Data Sources
- UBA vs. UEBA: Understanding the Entity Difference
- Critical Use Cases for Modern Security Ops
- Top 3 Benefits of UBA Deployment
- UBA-Enabled Adaptive Authentication
- Zero Trust and Behavior Analytics Alignment
- User Behavior Analytics FAQs
- What Is Active Directory (AD)?
- What Is Passwordless Authentication?
- What Is CIAM (Customer Identity and Access Management)?
-
Authentication and Authorization Explained
- Authentication and Authorization Explained
- Differentiating Authentication from Authorization
- Authorization Models: RBAC, ABAC, and Policy Enforcement
- Lateral Movement and Attacker Workflow
- Cloud Security Implications for Authorization
- Zero Trust Alignment with Access Control
- Authentication and Authorization FAQs
- What Is Single Sign-On (SSO)?
- What is BeyondCorp?
- What is the Evolution of Multifactor Authentication
- What Is Cloud Infrastructure Entitlement Management (CIEM)?
- What is Multifactor Authentication (MFA) Implementation?
- What Is Identity and Access Management (IAM)?
What Is Adaptive MFA and How Does It Work?
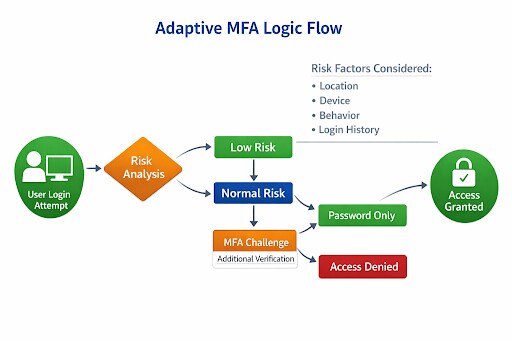
Adaptive multifactor authentication (adaptive MFA), also known as risk-based authentication, is an approach to authentication that adjusts verification requirements based on the context of a login attempt or transaction.
Rather than requiring the same authentication steps for every user in every scenario, adaptive MFA evaluates signals such as device posture, location, IP reputation, login behavior, and application sensitivity to determine the appropriate level of verification.
This approach helps organizations strengthen identity security while minimizing unnecessary friction for legitimate users. Low-risk access attempts may proceed with minimal interruption, while high-risk or anomalous activity can trigger additional verification or be blocked altogether.
Key Points
-
Contextual Analysis: Systems evaluate signals such as geo-velocity, IP addresses, and time of day to assess risk. -
Risk-Based Response: The system automatically steps up authentication requirements for high-risk attempts or streamlines low-risk logins. -
Reduced Friction: Legitimate users receive fewer prompts, minimizing MFA fatigue and improving daily productivity. -
AI Integration: Modern solutions leverage machine learning to establish behavioral baselines and detect subtle anomalies in real time. -
Zero Trust Alignment: Adaptive MFA supports a zero-trust architecture by continuously verifying identities in response to changing conditions.
How is Adaptive MFA Different from Traditional MFA?
Adaptive MFA is an authentication approach that uses risk analysis to determine whether a user should be granted access, asked for another factor, or blocked entirely.
- Traditional MFA applies the same policy to everyone.
- Adaptive MFA adds a decision layer: Is this login normal, or does it look suspicious? That makes it “adaptive.” The system responds to context.
A login from a managed laptop at a usual location during normal work hours may be considered low risk. A login from an unknown device, unusual geography, anonymizing network, or impossible-travel scenario may trigger step-up authentication, session limits, or outright denial.
OWASP describes this as authentication that dynamically adjusts its requirements based on the context of the login attempt.
Why Is Adaptive MFA Important?
Adaptive MFA matters because modern attacks do not politely stop at the password field.
Attackers use stolen credentials, session hijacking, MFA fatigue, adversary-in-the-middle phishing kits, token theft, and compromised devices. A flat authentication model creates two bad choices: either force everyone through constant prompts, or keep prompts light and accept more risk.
Adaptive MFA provides a middle path:
- less friction for normal access
- more scrutiny for suspicious access
- stronger protection for sensitive resources
That makes it especially useful for remote work, SaaS access, privileged accounts, third-party access, and hybrid environments where users, devices, and networks are constantly changing.
| Phase | Process | Description |
|---|---|---|
| Collect Context | Gather Signals | The authentication system collects real-time data about the request, including device posture, IP address, geolocation, browser details, login time, network reputation, and prior behavior. NIST cites IP addresses, geolocation, timing patterns, and browser metadata as key adaptive signals. |
| Calculate Risk | Assign Risk Score | A rules engine, analytics engine, or machine learning model evaluates the gathered signals to assign a risk score to the session. NIST guidance highlights risk-engine-based MFA that invokes stronger authentication specifically for higher-risk transactions. |
| Apply Policy | Determine Outcome | Based on the calculated risk score, the system executes a specific security response: allow access silently, require an additional factor, require a stronger factor, limit the session, or deny the attempt entirely. |
| Update Trust | Continuous Reassessment | Mature implementations move beyond initial login. They continuously reassess trust as user behavior changes during the session, particularly when the user attempts to access sensitive applications, data, or privileged actions. |
Adaptive MFA Use Cases & Real-World Examples
Securing the Remote Workforce
Remote workers often access business applications from diverse environments. An employee working from a home office on a recognized device may only need a password. However, if that same employee attempts to log in from a public Wi-Fi network in a different country, the system triggers a step-up challenge. This might include a biometric scan or a hardware token.
Critical Industry Access
In healthcare, clinicians require rapid access to patient records while maintaining strict compliance. Adaptive MFA allows a nurse to sign in once at the start of a shift with full MFA. For the remainder of the shift, the system may only require a simple proximity badge tap for subsequent logins on that specific terminal.
Unit 42 Research: Threat Actor Trends
Unit 42 research indicates that identity weaknesses play a material role in nearly 90% of incident investigations. Attackers now use AI to accelerate credential harvesting and bypass traditional local controls. Adaptive MFA serves as a critical barrier by detecting impossible travel scenarios where a user appears to log in from two distant locations simultaneously.
What are Adaptive MFA Best Practices?
| Implementation Step | Key Technical Action | Operational Benefit |
|---|---|---|
| Establish Baselines | Use AI/ML to profile normal user behavior over time. | Accurate anomaly detection. |
| Define Risk Rules | Set specific policies for roles, locations, and sensitive assets. | Customized security posture. |
| Integrate Threat Intel | Connect 3rd-party threat data to the authentication engine. | Proactive block lists. |
| Continuous Monitoring | Evaluate risk throughout the active session, not just at login. | Stops token theft in real time. |
What are Common Risk Signals Used by Adaptive MFA?
Adaptive MFA relies on the quality and relevance of the signals it evaluates. Common categories include:
Device Signals:
- managed versus unmanaged device
- known versus unknown device
- device health or compliance status
- suspicious browser or operating system changes
Network and Location Signals:
- source IP address
- geolocation
- impossible travel scenarios
- use of VPNs, proxies, or anonymizers
- network reputation
Behavioral Signals:
- unusual login times
- abnormal request volume or cadence
- deviations from typical user patterns
- anomalous interaction behavior
Access and Transaction Signals:
- sensitivity of the requested application or data
- role or privilege level of the user
- attempts to perform administrative or high-risk actions
- unusual transaction attributes
How is Adaptive MFA Related to Zero Trust?
Adaptive MFA is closely aligned with zero trust because both rely on continuous verification rather than inherited trust. A zero trust approach verifies identity, device, context, and policy before granting access to resources. Adaptive MFA strengthens that model by making authentication responsive to risk instead of static.
In practice, adaptive MFA often supports zero trust initiatives by helping organizations:
- Verify users more intelligently
- Reduce broad-standing access
- Protect sensitive applications
- Respond to anomalous behavior in real time
It is not the whole zero trust model, but it is one of the most practical controls for enforcing it.
What are Some Examples of Adaptive MFA in Action?
Adaptive MFA applies authentication controls based on the context and risk of each access attempt. The examples below illustrate how it can reduce friction for routine activity while requiring stronger verification for suspicious, privileged, or high-risk access scenarios.
| Example | Scenario | Risk Signals | Adaptive MFA Response |
|---|---|---|---|
| Low-risk employee login | An employee signs in from a managed device at the office during normal business hours using a known browser. The login pattern matches prior behavior. | Managed device, known browser, familiar location, normal business hours, consistent behavior | Allows access with minimal friction |
| Suspicious remote login | The same user attempts access from a new device in a different country two hours later. | New device, unusual location, impossible travel, abnormal access pattern | Requires a stronger second factor or blocks the request |
| Privileged admin action | An administrator logs in successfully, then attempts to disable logging and create a new privileged account. | Privileged activity, sensitive system changes, elevated access request | Triggers step-up authentication before allowing the action |
| Third-party access | A contractor accesses a sensitive application from an unmanaged device outside the approved maintenance window. | Unmanaged device, third-party user, sensitive application, access outside approved hours | Requires stronger verification and restricts session capabilities |
Adaptive MFA Transition Checklist
This technical MFA Implementation checklist is designed for SOC leaders and Network Architects to transition from static MFA to an Adaptive, risk-based model.
| Phase | Critical Action Item | Technical Requirement |
|---|---|---|
| Audit | Inventory existing MFA methods. | Identify all legacy hardware tokens and SMS-based systems. |
| Audit | Map high-value assets. | Categorize applications by sensitivity and data risk levels. |
| Design | Define baseline behavior. | Use AI to establish normal login hours and typical locations. |
| Design | Establish risk thresholds. | Set clear "step-up" triggers for unknown IPs or new devices. |
| Integration | Connect threat intelligence. | Feed Unit 42 or third-party threat data into the risk engine. |
| Integration | Enable geo-velocity rules. | Configure alerts for "impossible travel" between login attempts. |
| Deployment | Pilot with low-risk groups. | Test adaptive policies with a subset of users to tune accuracy. |
| Deployment | Implement phishing resistance. | Prioritize FIDO2 or biometric factors for high-risk challenges. |
| Monitoring | Monitor false positive rates. | Adjust the sensitivity if legitimate users frequently encounter challenges. |
| Monitoring | Review session persistence. | Set re-authentication intervals based on role and device health. |
Implementation Notes for SOC Leaders
- Phasing: Do not move the entire organization at once. Start with remote workers who frequently switch networks.
- Granularity: Use fine-grained policies. An IT Administrator should always face stricter adaptive rules than a standard retail associate.
- Continuous Loop: Use machine learning to refine your "normal" behavior profiles every 30 days. This accounts for seasonal travel or changes in office locations.