- What Is Access Management?
- What Is Access Control?
- What Is the Principle of Least Privilege?
-
What Is User Behavior Analytics (UBA)?
- User Behavior Analytics Explained
- How UBA Works: The Data-to-Insight Flow
- Core UBA Data Sources
- UBA vs. UEBA: Understanding the Entity Difference
- Critical Use Cases for Modern Security Ops
- Top 3 Benefits of UBA Deployment
- UBA-Enabled Adaptive Authentication
- Zero Trust and Behavior Analytics Alignment
- User Behavior Analytics FAQs
-
What Is Adaptive MFA? How Risk-Based Authentication Works
- How is Adaptive MFA Different from Traditional MFA?
- Why Is Adaptive MFA Important?
- How Does Adaptive MFA Work?
- Adaptive MFA Use Cases & Real-World Examples
- What are Common Risk Signals Used by Adaptive MFA?
- How is Adaptive MFA Related to Zero Trust?
- What are Some Examples of Adaptive MFA in Action?
- Adaptive MFA Transition Checklist
- Implementation Notes for SOC Leaders
- What Is Active Directory (AD)?
- What Is Passwordless Authentication?
- What Is CIAM (Customer Identity and Access Management)?
-
Authentication and Authorization Explained
- Authentication and Authorization Explained
- Differentiating Authentication from Authorization
- Authorization Models: RBAC, ABAC, and Policy Enforcement
- Lateral Movement and Attacker Workflow
- Cloud Security Implications for Authorization
- Zero Trust Alignment with Access Control
- Authentication and Authorization FAQs
- What Is Single Sign-On (SSO)?
- What is BeyondCorp?
- What is the Evolution of Multifactor Authentication
- What Is Cloud Infrastructure Entitlement Management (CIEM)?
- What is Multifactor Authentication (MFA) Implementation?
- What Is Identity and Access Management (IAM)?
What Is an Application Gateway?
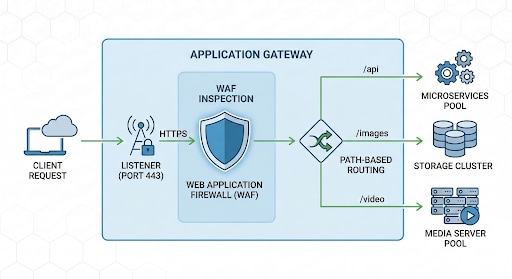
An application gateway is a Layer 7 load balancer that manages web traffic by making routing decisions based on the actual content of HTTP requests. It inspects application-level data, such as URL paths or cookies, to optimize delivery and security, acting as an intelligent reverse proxy for modern web applications.
Key Points
-
Layer 7 Visibility: Provides deep packet inspection to route traffic based on specific application-level attributes rather than just IP addresses. -
Traffic Orchestration: Sophisticated routing rules allow for complex architectures, including multi-site hosting and URL-path-based redirection from a single entry point. -
Security Integration: Functions as a robust security perimeter by integrating Web Application Firewall (WAF) capabilities to block common exploits like SQL injection. -
Scalable Performance: Enhances backend efficiency by terminating SSL/TLS and offloading heavy encryption tasks from application servers to the gateway. -
Protocol Support: Optimized specifically for web-based protocols, including HTTP, HTTPS, and WebSocket, to support modern, interactive digital experiences.
App Gateway Explained: Beyond Basic Load Balancing
Traditional load balancers operate at Layer 4, handling traffic based on network protocols like TCP or UDP. An application gateway operates at Layer 7, providing deep visibility into the HTTP/HTTPS payload. This distinction is vital for security leaders as they move away from legacy hardware toward cloud-native architectures.
By acting as a reverse proxy, the gateway terminates the client connection and opens a new one to the backend. This creates a secure buffer between the public internet and your private infrastructure. It allows for "content-aware" routing, where the gateway sends traffic to different server pools based on the request's intent.
How Does an Application Gateway Work?
The process begins when a client sends a request to the gateway's public IP. The gateway evaluates this request through a series of logical checks before passing it to the appropriate backend resource.
The Anatomy of a Request: Listener to Backend Pool
Listeners monitor specific ports and protocols for incoming traffic. When a request arrives, the gateway applies routing rules to determine the destination.
| Component | Function |
|---|---|
| Listener | Checks for traffic on specific ports (e.g., 80 or 443). |
| Routing Rule | Defines where to send traffic based on URL path or host headers. |
| Backend Pool | The group of servers or containers that process the request. |
| Health Probe | Periodically checks if backend servers are online. |
Key Benefits and Strategic Advantages
Centralizing traffic management provides several operational wins. It simplifies certificate management and ensures uniform security policies across all hosted services.
- Enhanced Security: Inspects traffic for malicious patterns before it reaches the application code.
- SSL Offloading: Handles encryption tasks at the edge, freeing up backend CPU cycles.
- Connection Draining: Allows for graceful server maintenance by completing active sessions while blocking new ones.
Application Gateway vs. Traditional Tools
Understanding the difference between network-level and application-level tools helps architects select the right defense-in-depth components.
Comparison: Layer 4 vs. Layer 7
| Feature | L4 Load Balancer | Application Gateway (L7) |
|---|---|---|
| OSI Layer | Layer 4 (Transport) | Layer 7 (Application) |
| Routing Logic | IP and Port | URL, Headers, Cookies |
| Visibility | Packet-level only | Full HTTP payload |
| Primary Use | High-speed packet switching | Complex web app delivery |
Why Gateways Support Zero Trust
Legacy VPNs often grant broad network access, creating significant security risks. Application gateways align with zero trust principles by providing "per-app" access. Users can access only the specific application they are authorized for, significantly reducing an attacker's lateral movement capabilities.
Implementation Challenges and Solutions
Deploying a gateway requires balancing security rigor with user performance.
- Certificate Management: Centralized SSL termination requires rigorous tracking of expiration dates to avoid site-wide outages.
- Probe Accuracy: Health probes must be configured to check actual application logic, not just network connectivity.
- Latency Management: Deep packet inspection adds overhead; teams must optimize WAF rules to maintain speed.
Advanced Proactive Defense
Modern threats move faster than manual defenses can react. According to Unit 42 research, attack speeds have increased significantly, with many exploits occurring within hours of a vulnerability disclosure. Integrating real-time threat intelligence into the gateway's WAF allows for automated blocking of known malicious actors.