Why Access Certification Matters
Access is one of the most common paths to compromise. Attackers do not always need to break in if they can log in using valid credentials, hijack an overprivileged account, or abuse standing permissions that were never removed.
That makes access certification a practical identity security control, not just an administrative exercise.
When access certification is weak or inconsistent, organizations often face familiar problems:
- Former employees retain access after departure
- Users keep privileges from prior roles
- Contractors retain access long after projects end
- Sensitive applications accumulate too many approved users
- Privileged access is granted broadly and rarely reviewed
- Service accounts operate with little visibility or ownership
- Toxic combinations of access create segregation-of-duties risk
A strong certification program helps organizations reduce these issues before they turn into incidents, audit findings, or operational failures.
How Access Certification Works
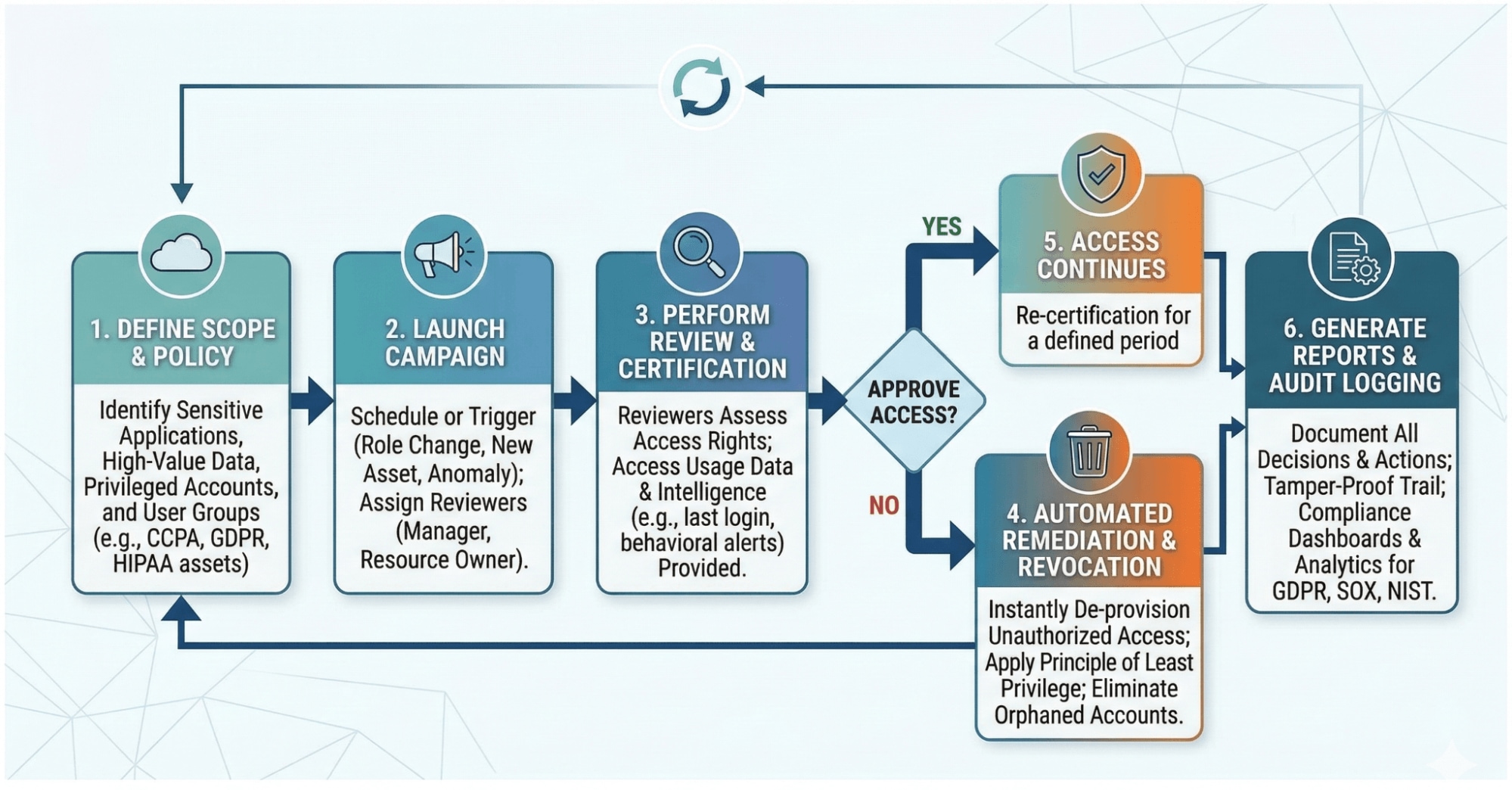
At a high level, access certification is a structured review cycle. The organization identifies a set of users, roles, systems, or entitlements to review, assigns reviewers, and requires them to approve, revoke, or modify access based on current business needs.
A typical access certification process includes the following steps:
1. Define the Scope
The organization determines what will be reviewed. This may include:
- User accounts
- Group memberships
- Application entitlements
- Privileged roles
- Shared accounts
- Service accounts
- Third-party access
- Cloud permissions
- Sensitive data access
Some reviews focus on a single application. Others span departments, roles, or enterprise-wide privileged access.
2. Assign Reviewers
Reviews are typically performed by managers, application owners, data owners, or system owners. In some cases, reviewers may be responsible for certifying access for:
- Their direct reports
- Users of a specific system
- Access to regulated data
- Privileged administrators
- External vendors and partners
The right reviewer is the person best positioned to decide whether access is still justified.
3. Present Access Data
Reviewers receive a list of users and their current permissions. The quality of this step matters. If the access data is incomplete, unclear, or filled with technical jargon, reviewers may approve access blindly.
Effective certification campaigns present:
- The user’s name and role
- The application or system
- The specific entitlement or privilege
- The business context for the access
- Risk indicators, where available
- Last-used data, where available
- Ownership and justification details
Good certification depends on understandable data. Otherwise, the review becomes theater.
4. Review and Decide
The reviewer evaluates whether each access right should remain in place. Common outcomes include:
- Approve: Access is still needed
- Revoke: Access is no longer needed
- Modify: Access should remain, but at a different level
- Reassign: The reviewer cannot determine the appropriate action and routes it elsewhere
This stage should be based on business necessity, role alignment, and risk, not habit or convenience.
5. Remediate Changes
Once decisions are made, revocations and changes must be carried out. This is where many programs fall short. A review that identifies unnecessary access but never removes it is not much of a control.
Mature programs connect certification outcomes to automated remediation workflows, so approved changes are enforced consistently.
6. Record Results for Auditability
Organizations need evidence that reviews occurred, who completed them, what decisions were made, and when remediation was performed. This creates an auditable trail and helps demonstrate compliance.
Types of Access Certification
Not every certification campaign looks the same. Organizations usually combine several review types depending on risk, system criticality, and compliance needs.
Manager Certification
Managers review the access held by their direct reports. This is one of the most common certification methods because managers usually understand whether an employee still needs access to perform their job.
Application Owner Certification
Application owners review who has access to a particular application or platform. This works well for business-critical systems like ERP, CRM, finance, HR, or security tools.
Role-Based Certification
The organization reviews role definitions and the entitlements assigned to each role. This helps ensure that roles remain aligned with real job functions and do not accumulate unnecessary privileges over time.
Privileged Access Certification
High-risk accounts with administrative or elevated privileges receive focused review. Because privileged accounts have a disproportionate impact, these reviews are often more frequent and more tightly controlled.
Event-Driven Certification
Certification is triggered by a specific event, such as:
- Role change
- Department transfer
- Termination
- Merger or acquisition
- New application onboarding
- Policy violation
- Risk detection
This is often more effective than relying only on annual campaigns.
Compliance-Driven Certification
Some reviews are scheduled specifically to support regulatory or internal control requirements for access to financial systems, customer data, health data, or critical infrastructure.
What Access Certification Reviews
Access certification can cover a wide range of identities and permissions, including:
Use Cases & Real-World Examples
Unit 42 research highlights that nearly half of all successful intrusions involve compromised credentials. Attackers frequently exploit "orphaned" accounts belonging to former employees to gain a foothold. Access certification acts as a proactive defense by ensuring these accounts are revoked immediately upon termination.
In cloud environments, machine identities outnumber human identities by 82 to 1. Unit 42 investigators found that identity misconfigurations played a material role in almost 90% of investigations in 2025. Regular access certification helps security teams detect these "invisible" over-permissioned service accounts before they are exploited for large-scale data exfiltration.
Access Certification vs. Access Review
The terms are closely related and sometimes used interchangeably, but they are not always identical.
An access review is the broader act of examining permissions. An access certification usually refers to a more formal, governed review process with documented attestation and auditable outcomes.
In practice:
- An access review can be informal or operational
- An access certification is typically structured, recurring, and auditable
That formal element is what makes certification especially important in governance and compliance programs.
Access Certification vs. Provisioning
Provisioning grants access. Certification validates whether that access should continue.
These processes are related but serve different purposes:
Without certification, provisioning tends to move in one direction: more access, more exceptions, more risk.
Access Certification and Least Privilege
Least privilege means giving identities only the minimum access required to perform approved tasks. Access certification is one of the primary ways organizations maintain least privilege over time.
That matters because access environments change constantly. People change jobs. Applications evolve. Teams inherit responsibilities. Emergency access becomes permanent. A permission that made sense six months ago may be completely unjustified today.
Certification helps correct those mismatches by forcing periodic revalidation of access decisions.
In that sense, access certification is not separate from least privilege. It is one of the mechanisms that help ensure least privilege is not just a slogan but a reality.
Common Access Certification Challenges
Many organizations claim to perform access certification. Far fewer do it well. The usual obstacles are not mysterious.
Poor Data Quality
If reviewers cannot understand what an entitlement means, they cannot make a sound decision. Ambiguous group names, missing ownership, and incomplete context lead to rubber-stamp approvals.
Too Many Manual Reviews
Large enterprises may have thousands of applications and millions of entitlements. Manual spreadsheets and email-based campaigns do not scale.
Review Fatigue
When reviewers are asked to approve large volumes of access with little context, they often click through the process as quickly as possible. That creates the appearance of control without the substance.
No Risk Prioritization
Not all access is equally important. Reviewing low-risk access with the same urgency as domain admin privileges does not waste time or attention.
Weak Remediation
Identifying inappropriate access is only half the job. If revocation is slow, inconsistent, or disconnected from the review process, risk remains in place.
Limited Visibility into Non-Human Identities
Service accounts, API keys, machine identities, and application-to-application permissions are often underreviewed even though they can carry significant privilege.
Access Certification Best Practices
Implementing a resilient access certification program requires a strategic shift from manual, "check-the-box" exercises to automated, risk-based workflows. Effective certification ensures that user permissions remain strictly aligned with current job functions while minimizing the burden on business managers.
By following these industry best practices, organizations can strengthen their security posture, simplify regulatory audits, and eliminate the hidden risks associated with privilege creep.
Access Certification Best Practices
Access Certification and Compliance
Access certification plays a major role in many compliance and audit programs because organizations must demonstrate that access to sensitive systems is reviewed and controlled.
Depending on the environment, certification can help support requirements related to:
- Financial controls
- Privacy and data protection
- Healthcare data access
- Internal governance standards
- Segregation of duties
- Privileged access oversight
- Audit readiness
Auditors often want evidence that access is granted appropriately, reviewed regularly, and removed when no longer needed. Certification helps provide that proof. Still, compliance is not the whole story. A program built solely to satisfy auditors often becomes a paperwork exercise. A good program supports both compliance and actual risk reduction.
How Access Certification Supports Identity Security
Identity has become a primary control plane in enterprise security. That means access certification now sits closer to security operations than many organizations once assumed.
Certification supports identity security by helping organizations:
- Reduce standing access
- Detect overprivileged identities
- Limit lateral movement opportunities
- Govern privileged and third-party access
- Strengthen zero trust principles
- Improve visibility across human and non-human identities
In mature security models, access certification is not isolated inside HR or compliance workflows. It connects with broader controls such as privileged access management (PAM), identity threat detection and response (ITDR), role governance, and lifecycle management.
Signs Your Access Certification Process Needs Improvement
A certification process likely needs work if any of the following are true:
- Reviews are done mainly in spreadsheets
- Managers approve everything by default
- Revocations take weeks or months
- Service accounts are not reviewed
- Third-party access is poorly tracked
- Entitlement names are confusing or meaningless
- Reviews happen only once a year
- Audit evidence is difficult to produce
- Users retain access after internal transfers
- Privileged access is broadly approved without challenge
That is not governance. That is drift with paperwork attached.
The Future of Access Certification
Access certification is moving away from static, periodic review cycles toward more continuous and risk-aware models.
That shift includes:
- Greater use of automation and AI
- More event-driven reviews
- Better visibility into SaaS and cloud entitlements
- Better visibility into AI agent identities
- Integration with identity security platforms
- Stronger focus on machine identities and service accounts
- Risk-based decision support for reviewers
- Tighter connection to least privilege and Zero Trust programs
The old model of annual blanket review campaigns is increasingly inadequate for environments shaped by cloud, SaaS, APIs, contractors, automation, and distributed workforces.
Organizations need certification that is timely, contextual, and enforceable.
Access Certification FAQs