- Machine Identity Security: The Definitive Guide
- What Is Workload Identity? Securing Non-Human Identities
- What Is a Non-Human Identity (NHI)? Machine Identity Security Explained
- What is Code Signing? Benefits, Risks & Implementation
- What Is a TLS Decryption? Methods, Risks & Best Practices
- What Is a TLS Certificate? How TLS Secures Web Communication
- What Is a TLS/SSL Port? Port 443 and HTTPS Explained
- What Is a Self-Signed Certificate? Risks, Uses & Best Practices
-
What Is TLS Certificate Renewal? Process, Risks & Automation
- TLS Certificate Renewal: The Shift from Maintenance to Mission-Critical
- Why the 47-Day Mandate Redefines Renewal Strategy
- The Technical Lifecycle of a TLS Renewal
- Critical Risks: The High Cost of Renewal Failure
- Best Practices for Enterprise-Scale Renewal
- Overcoming Common Renewal Challenges
- TLS Certificate Renewal FAQs
- What Is PKI? Public Key Infrastructure & Authentication Guide
-
What Is the TLS Handshake? Process, Steps, and Best Practices
- The Strategic Importance of the TLS Handshake
- How the TLS Handshake Works: Step-by-Step
- TLS 1.2 vs. TLS 1.3: Evolution of Speed and Security
- The Role of Cipher Suites and Digital Certificates
- Identifying and Resolving TLS Handshake Failures
- Advanced Security: TLS Fingerprinting and Threat Detection
- TLS Handshake Best Practices
- TLS Handshake FAQs
-
What Is the TLS Certificate Lifecycle? Implementation Guide
- TLS Certificate Lifecycle Explained
- The 6 Core Stages of the TLS Certificate Lifecycle
- Why TLS Certificate Lifecycle Matters
- Key Causes of Certificate Failure
- Validation Checks: CRL and OCSP
- How Automation Improves TLS Certificate Lifecycle
- TLS Certificate Lifecycle and Zero Trust
- TLS Certificate Lifecycle FAQs
- What Is Certificate Management?
-
What Is Cert-Manager? Kubernetes Certificate Management Explained
- cert-manager Explained
- Core Components: Issuers and Certificates
- 1. Issuers and ClusterIssuers
- 2. Certificates
- How cert-manager Automates Machine Identity
- Common Compatible Cloud Platforms
- Zero Trust and Kubernetes Security Alignment
- Integrating cert-manager into DevSecOps Workflows
- Benefits for DevSecOps Teams
- cert-manager FAQs
-
TLS/SSL Offloading: Definition & Decision Checklist
- TLS/SSL Offloading Explained
- SSL Termination vs. SSL Bridging
- Key Differences in Workflow
- Unit 42 Perspective: Risks of Uninspected Traffic
- Benefits for Security and Infrastructure Teams
- CISO Decision Checklist: SSL Termination vs. SSL Bridging for Compliance
- Detailed CISO Decision Checklist
- Summary Recommendation for CISOs
- TLS/SSL Offloading FAQs
-
What Is Certificate Validation? Guide to Best Practices
- Certificate Validation Explained
- The Role of Certificate Authorities and the Chain of Trust
- The Hierarchy of Trust
- The Sequence of the Validation Process
- Types of Certificate Validation Levels
- Unit 42 Insights: The Risk of Identity Exposure
- Threat Behavior Observations
- Troubleshooting Common Validation Failures
- Certificate Validation FAQs
-
What Is Certificate Pinning? Benefits, Risks & Best Practices
- Certificate Pinning Explained
- How Certificate Pinning Works
- Listiche: Key Stages of a Pinning Failure
- Types of Certificate Pinning
- Listiche: Static vs. Dynamic Pinning
- Why Pinning Is Essential for Zero Trust
- Certificate Pinning vs. Standard SSL/TLS
- Benefits of Certificate Pinning
- Risks and Limitations of Certificate Pinning
- When to Use Certificate Pinning
- When to Avoid Certificate Pinning
- Certificate Pinning Best Practices
- Certificate Pinning and Machine Identity Security
- FAQs
- What is Cloud Workload Security? Protection & Best Practices
- What Is ACME Protocol?
-
What is SPIFFE? Universal Workload Identity Framework Guide
- SPIFFE Explained: Solving the Workload Identity Problem
- Core Components of the SPIFFE Standard
- The SPIFFE Workload API
- Why Traditional Secret Management Fails in Cloud-Native Environments
- The Problem of "Secret Zero"
- Vulnerabilities of Static Credentials and Long-Lived Tokens
- IP-Based Security vs. Identity-Based Security
- How SPIFFE Implementation Works: The Attestation Process
- The Role of SPIRE as the Reference Implementation
- Critical Use Cases for Enterprise Security
- SPIFFE FAQs
- What Is an SSL Stripping Attack?
-
What Is a Machine Identity?
- How Do Machine Identities Work?
- Machine Identity Management (MIM) vs. Human IAM
- Architecture Components and Identity Types
- Secrets Management vs. Machine Identity Management
- Lateral Movement and Attacker Workflow
- Cloud Security Implications and CIEM
- Implementation Steps for Machine Identity Security
- Machine Identity FAQs
What Is An X.509 Certificate?
An X.509 certificate is a digital document that uses the international X.509 public key infrastructure (PKI) standard to verify that a public key belongs to a specific user, computer, or service. It serves as a digital passport, enabling secure communication through encryption and authentication across the internet and private networks.
Key Points
-
Identity Verification: Validates the ownership of public keys by specific entities. -
Standardized Structure: Follows a strict format defined by the ITU-T to ensure global interoperability. -
Trust Anchor: Relies on a Certificate Authority (CA) to sign and vouch for the identity. -
Encryption Foundation: Forms the basis for SSL/TLS protocols, securing web traffic. -
Binding Mechanism: Securely binds a distinguished name to a public key. -
Lifecycle Management: Includes expiration dates and revocation mechanisms to maintain security.
X.509 Certificates Explained
X.509 is the cornerstone of Public Key Infrastructure (PKI). While many people associate these certificates solely with the "padlock" icon in a web browser, their utility extends far beyond website security. The standard defines the format for public-key certificates, attribute certificates, and certificate revocation lists (CRLs).
An X.509 certificate uses asymmetric cryptography. Every certificate is paired with a private key that is kept secret by the owner. The certificate itself contains the public key, which anyone can see.
When a client connects to a server, the server presents its X.509 certificate. The client then checks the digital signature on that certificate. If the signature is valid, the issuing CA is trusted, the certificate's subject or SAN matches the expected hostname, and the certificate is within its validity period, the client can trust the connection.
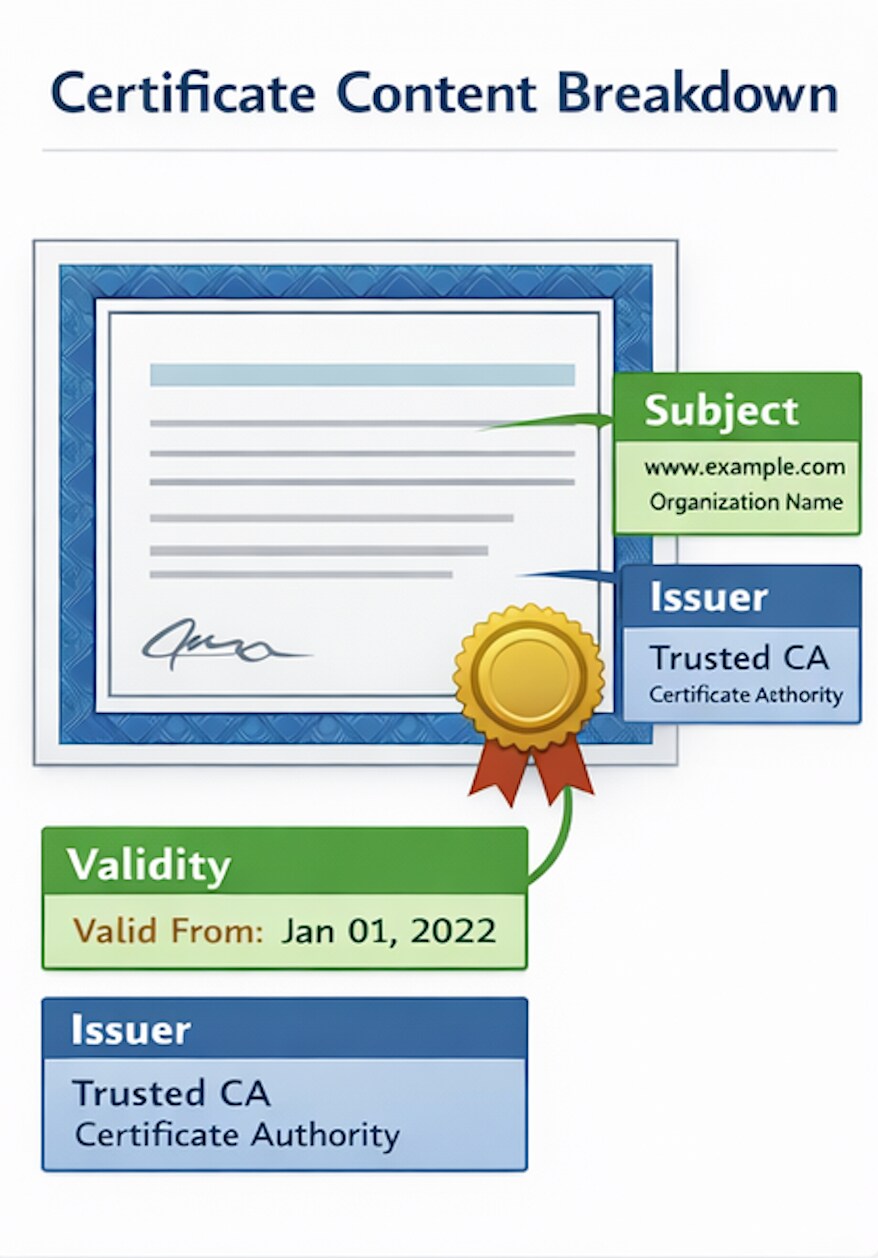
The Anatomy Of An X.509 Certificate
To ensure that different systems can read and process identity data, the X.509 standard requires a specific set of fields. Modern certificates generally follow the v3 format, which allows for custom extensions.
X.509 Certificate Fields
| Field | Description |
|---|---|
| Version | Identifies which X.509 version applies (typically v3). |
| Serial Number | A unique identifier assigned by the CA to distinguish the certificate. |
| Signature Algorithm | The algorithm used by the CA to sign the certificate (e.g., SHA-256 with RSA). |
| Issuer | The name of the entity (CA) that verified the information and issued the certificate. |
| Validity Period | The "Not Before" and "Not After" dates define the certificate's life. |
| Subject | The identity of the entity the certificate represents (e.g., a domain name). |
| Public Key | The actual public key and its associated algorithm (RSA, ECC, etc.). |
Important X.509 v3 Extensions
While the standard X.509 fields provide the basic identity framework, the v3 extensions enable these certificates to meet the complex requirements of modern digital ecosystems.
These extensions provide the flexibility to add additional attributes, such as alternative hostnames, specific usage constraints, and policy identifiers, that guide how an application or operating system should process and trust the certificate.
By defining these extra layers of metadata, organizations can tailor certificates for highly specific roles, from securing a single web server to authenticating millions of IoT devices:
- Subject Alternative Name (SAN): Allows a certificate to secure multiple hostnames.
- Key Usage: Defines the technical purpose of a key, such as digital signature or key encipherment.
- Extended Key Usage (EKU): Provides specific purposes, such as server authentication or code signing.

The X.509 Trust Hierarchy And Chain
Trust is not inherent in an X.509 certificate; it is inherited from a parent entity. This creates a chain of trust.
- Root Certificates: Self-signed certificates owned by a certificate authority that are pre-installed in "trust stores" on operating systems and browsers.
- Intermediate Certificates: Act as buffers between the root and the end-user. If an intermediate certificate is compromised, the root remains safe.
- End-Entity Certificates: Certificates that are issued to your website, server, or device.
When a device validates a certificate, it follows the chain of signatures up to a trusted root. This process is essential for maintaining cloud security and preventing attackers from spoofing identities through lateral movement.
Common Uses For X.509 Standard Certificates
The X.509 standard is versatile, supporting a range of security requirements across the enterprise.
- Web Security (SSL/TLS): The most visible use is protecting data in transit between browsers and servers.
- Email Encryption (S/MIME): Allows users to digitally sign and encrypt emails to prevent tampering.
- Code Signing: Software developers use certificates to sign their applications, proving the code has not been altered by a third party.
- Client Authentication: Instead of passwords, systems use certificates to identify users or machines trying to access a network.
- Secure Boot: Firmware verifies digital signatures on bootloaders and OS components using trusted keys, often stored as X.509 certificates in the UEFI key database.
Machine Identity And Management Challenges
In the era of microservices and IoT, the number of machines requiring identities has exploded. Every container, virtual machine, and smart device needs a unique X.509 certificate to participate in a secure network.
Unit 42 research indicates that many organizations struggle with "certificate sprawl," in which unmanaged or expired certificates cause service outages.
Risks Of Poor Certificate Management
- Outages: Expired certificates cause browsers to block sites and keep applications from communicating.
- Compromised Keys: If a private key is stolen, an attacker can impersonate the machine and escalate privileges
- Weak Algorithms: Older certificates that use deprecated algorithms, such as SHA-1, are vulnerable to collision attacks.
To mitigate these risks, organizations should scope certificates narrowly: limit Subject Alternative Names, constrain Key Usage and Extended Key Usage, and apply least privilege to the identities those certificates represent.
Zero Trust And X.509 Alignment
X.509 certificates are fundamental to a zero trust architecture. In a zero trust model, "trust nothing, verify everything" is the rule. This requires strong identity security for every connection.
How Does X.509 Support Zero Trust?
In a Zero Trust architecture, the traditional "castle-and-moat" security model is replaced by a philosophy of continuous verification. Because Zero Trust assumes that the network is already compromised, it requires every user, device, and application to prove its identity before granting access to resources.
X.509 certificates are one of the most widely used mechanisms for this verification, providing standardized, cryptographic identity proof and encrypted communications. By moving security controls away from static IP addresses and toward dynamic, certificate-based identities, organizations can build a more resilient defense against modern threats.
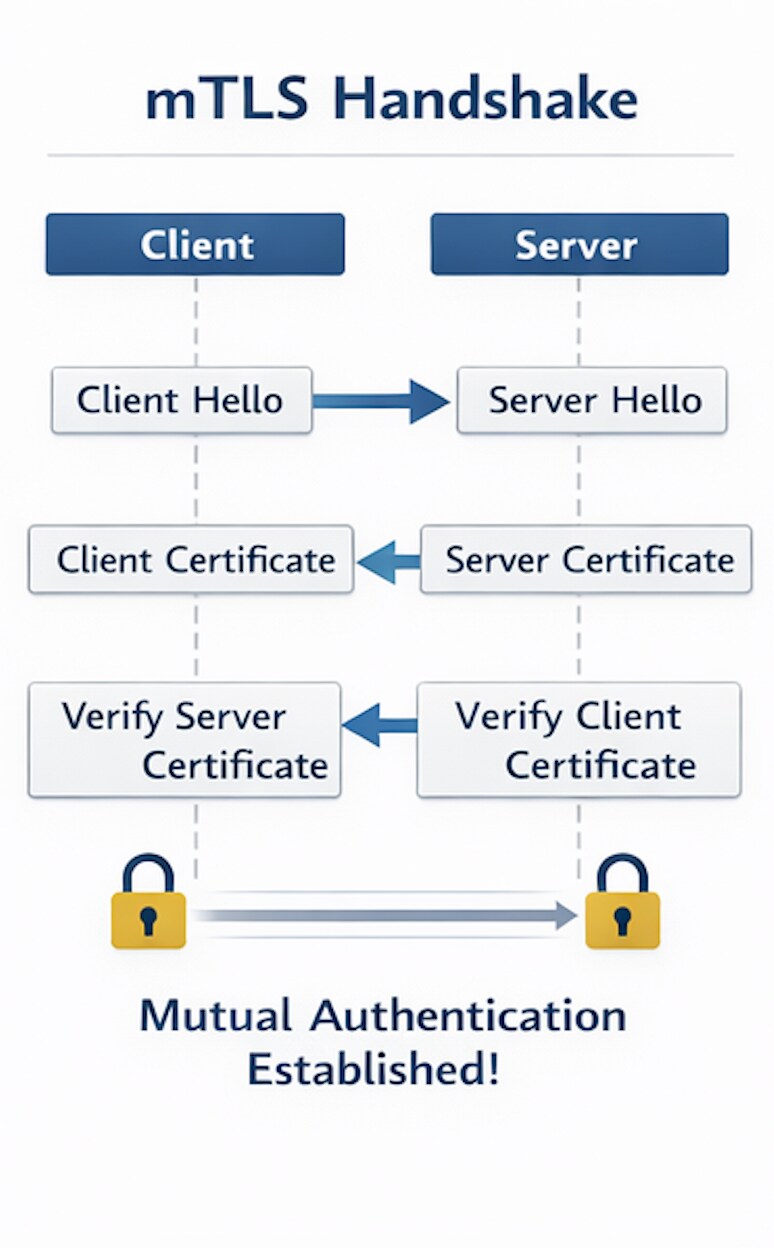
- Mutual TLS (mTLS): Both the client and the server must present certificates to each other. This ensures that both parties are authenticated before any data is exchanged.
- Microsegmentation: By using certificates to identify specific workloads, security teams can enforce network segmentation policies that prevent unauthorized lateral movement between servers.
- Short-Lived Certificates: Reducing the validity period of certificates minimizes the window of opportunity for an attacker if a key is compromised.
| Traditional Trust | Zero Trust with X.509 |
|---|---|
| Trust based on network location (IP address). | Trust based on verified digital identity. |
| Long-lived, static credentials. | Short-lived, automated certificate rotation. |
| One-way authentication (server only). | Mutual authentication (mTLS). |