Governments, organizations and businesses are readily embracing transformation at the edge of mobile networks these days. Mobile edge — with its distributed support for low latency, capacity for rapid delivery of massive data amounts, and scalable cloud-native architectures — enables mission critical industrial and logistic applications and creates richer experiences across remote working, education, retail and entertainment. Bringing resources closer to the user creates a better user experience, serving mission critical applications and taking advantage of improved economics.
But, mobile edge, including Multi-access Edge Computing (MEC), requires a new kind of approach to cybersecurity. It is a new environment where the network, applications and services are not only distributed geographically but also across organizational boundaries. Service providers’ 5G infrastructure and enterprise networks will be deeply intertwined. Further, the mobile edge will be highly adaptive. It will dynamically scale to meet demands of new applications and changing usage patterns.
Effective 5G edge security is best achieved through a platform approach that combines the protection of diverse mobile edge environments under one umbrella. A platform approach not only provides visibility for advanced, network-wide threat detection but it provides the necessary foundation for security automation. Automation is vital for security to keep up with the dynamically changing 5G environment.
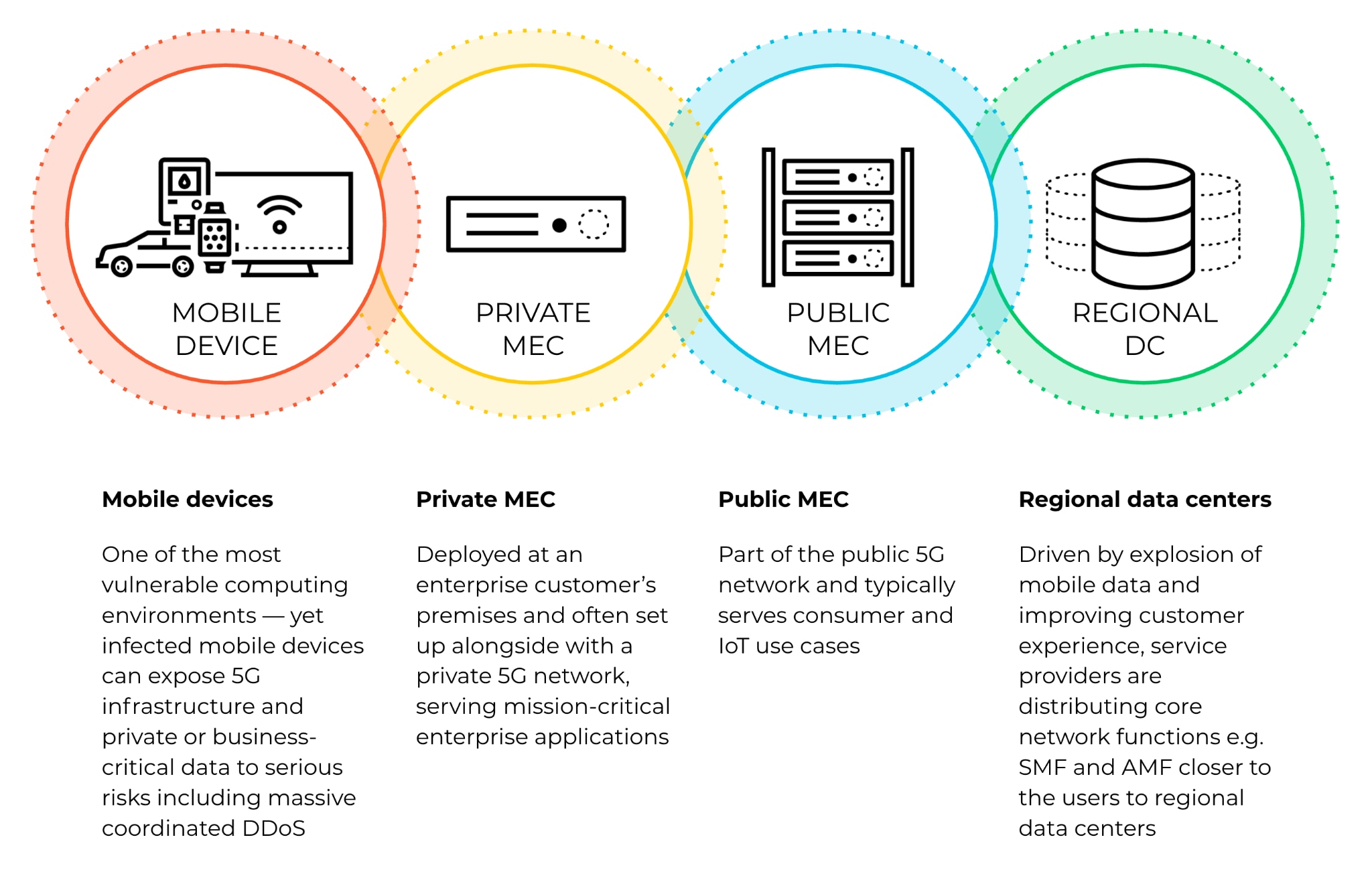
We can think of 5G networks to include four types of edge environments. Effective edge security spans across all of these environments.
Regional data centers — protect distributed core network with distributed security
Driven by explosion of mobile data and improving customer experience, service providers are distributing core network functions — e.g., Session Management Function (SMF) and Access and Mobility Management Function (AMF) — closer to the users to regional data centers. Service providers are able to improve user traffic latency and can optimize their transport architecture for cost savings.
As network functions — e.g., SMF and AMF — are brought to the edge of the network, securing them needs to take place there, as well. Instead of providing protection at one to three national data centers, it now needs to be implemented at five to ten regional data centers. The key interfaces to protect are N2 and N4. Unprotected N2 interfaces can be vulnerable to Radio Access Network (RAN) based threats from gNodeB base stations (gNBs). Unprotected N4 interfaces can be vulnerable to Packet Forwarding Control Protocol (PFCP) threats between distributed user plane function (UPF) — e.g. located in a MEC environment — and the core network.
Additionally, SMF, AMF and other network function workloads need protection in this typically cloud-native container-based environment.
The key for protecting the regional data center environment is a cloud-native security platform that can be automatically scaled to changing traffic or topology demands. At the same time, many of the threats are telco specific and preventing them requires built-in support for the telco protocols.
Public MEC — support user experience with cloud-native security
Public MEC is part of the public 5G network and typically serves consumer and IoT use cases. It integrates applications as part of the 5G network and brings them closer to the user. This improves the user experience while also optimizing the cost by deploying resources where they are needed. Public MEC is built into the service provider’s network by utilizing a distributed user plane function (UPF) to directly break out traffic to edge applications. Many service providers are partnering with cloud service providers (CSPs) on building these application environments as the CSP platforms have become the standard.
As third party applications become an integral part of the 5G networks, protecting and monitoring the application workloads and protecting UPF with microsegmentation promotes stopping any lateral movement of attacks.
Edge applications are also integral to the 5G user experience. Smoothly working applications — for example, video content, AR/VR and gaming — promote service providers’ customer retention rate.
Securing the public MEC calls for a cloud-native, multi-cloud approach for cloud workloads and microsegmentation.
Private MEC — empower enterprises with full control over 5G traffic
Private MEC is deployed at an enterprise customer’s premises and is often set up alongside with a private 5G or LTE network, serving mission-critical enterprise applications. It utilizes a local UPF to break out user plane traffic to the enterprise network. The traffic is further routed to a low-latency edge application or deeper into the enterprise network. A key driver for private MEC adoption is privacy of the traffic — an enterprise has full control of its 5G traffic, which never leaves its environment.
Private MEC carries the enterprise customer’s data. In today’s distributed world with eroded security perimeters, many enterprises rely on the Zero Trust approach to protect their users, applications and infrastructure. A critical building block for implementing a Zero Trust Enterprise is the ability to enforce granular security policies and security services across all network segments — including 5G traffic. Service providers need to find ways to empower enterprise customers with full control over the 5G traffic.
At the same time, the service provider needs to securely expose interfaces from the customer’s premises to their core network — namely the N4 interface to SMF for PFCP signaling traffic originating from the private MEC.
Private MEC security requires a flexible approach to bring security to heterogeneous private MEC environments across appliance, virtual and cloud environments. Many enterprises will choose to leverage partners for turnkey private MEC solutions and they will be requiring built-in security. Also cloud service providers are going after the private MEC market and the ability to provide cloud-native security will be critical.
Mobile devices — most effectively protected with network based security solutions
Accelerated by rapidly increasing IoT devices, the number of mobile devices is massive. The devices are heterogeneous across a multitude of software and hardware platforms. The limited computing and battery capacity of these devices often forces the device vendors to make compromises in security capabilities, making mobile devices a soft target. Infected devices can compromise organizations’ business critical data and disturb mission-critical operations. They also pose a risk to the mobile network itself, especially in case of botnet-originated massive coordinated DDoS attacks.
The combination of limited device resources, heterogeneous device types and device vendors’ tight control of the platforms makes it difficult to to implement device-based security solutions in scale. Network-based security, on the other hand, is a highly effective method to protect mobile devices at scale. When supported with granular visibility to user (SUPI) and device (PEI) level traffic flows, network-based security can see and stop advanced threats in real time. Organizations are able to protect their mobile devices across attack vectors including vulnerability exploits, ransomware, malware, phishing and data theft.
Network-based security can be deployed as part of any of the edge environments or the service provider’s core network.
Staying on top of privacy in distributed 5G networks
Protecting private information is more important than ever. Handling of private information is heavily regulated and breaches can result in public backlash. As the mobile core network becomes more distributed, the service providers need to double down on protecting Customer Proprietary Network Information (CPNI) that is now often carried in the signaling traffic (e.g., N4) between MEC sites and regional and national data centers. Service providers often use encryption to protect CPNI.
Conclusion
Securing the 5G edge requires a zero trust approach that can scale across multiple different environments. The distributed 5G network no longer has a clear perimeter. Service providers’, enterprises’ and CSPs’ assets and workloads are intertwined. Only through visibility and control across the whole system, can service providers and enterprises detect breaches, lateral movement, and stop the kill chains.
The new mobile networks are complex, but securing them doesn’t need to be. The key for simple 5G edge security is a platform approach that manages protecting the key 5G interfaces under a single umbrella — no matter if they are distributed across private and public telco clouds and data centers.
Learn more about Palo Alto Networks 5G-Native Security for protecting 5G interfaces, user traffic, network function workloads and more. Our ML-Powered NGFW for 5G provides deep visibility to all key 5G interfaces and can be deployed across data center (PA-Series), virtual (VM-Series) and container-based (CN-Series) environments. Our Prisma Cloud Compute provides cloud-native protection for container-based network function (CNF) workloads.