The expanding number of IoT devices, while enhancing business productivity, has created an increasing amount of access points for attackers to exploit. As organizations continue to adopt IoT technologies, it’s imperative they employ strict security measures to decrease the attack surface and prevent potential threats. This blog post identifies a series of IoT threats organizations may be exposed to and the proper mitigation strategies they can employ to secure IoT devices and protect sensitive data.
Cybersecurity researchers at JSOF recently published a number of zero-day vulnerabilities in the TCP/IP protocol library developed by Treck. This library, which implements a lightweight TCP/IP stack, has been used by multiple vendors as a way of providing internet connectivity across a number of different device types. The collection of threats, given the name Ripple20, constitute 19 vulnerabilities that can allow an attacker to execute code remotely, steal data, change behavior, cause malfunctions, and hide malicious code. Four of these vulnerabilities are of critical severity, with CVSS scores above nine. The attacks can be performed over DNS, ICMP, DHCP, IPv6, and ARP.
Ripple20 is especially significant due to the number of vendors, devices, and verticals that use the aforementioned library. As per the researchers at JSOF, the vulnerabilities have been named this way to signify the ripple effect they will cause in the IoT landscape over the next several years.
Ripple20 Vulnerability Overview
The following table lists the severity and fixed version for each Ripple20 CVE (common vulnerability and exposure):
| CVE | Severity | Component Affected | Potential Impact | Fixed Version |
| CVE-2020-11896 | Critical | IPv4/UDP | Remote Code Execution | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11897 | Critical | IPv6 | Remote Code Execution | Treck TCP/IP 5.0.1.35 |
| CVE-2020-11898 | Critical | IPv4/ICMPv4 | Out-of-Bounds Read | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11899 | Medium | IPv6 | Out-of-Bounds Read | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11900 | High | IPv4 | Use After Free | Treck TCP/IP 6.0.1.41 |
| CVE-2020-11901 | Critical | DNS | Remote Code Execution | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11902 | High | IPv6/IPv4 | Out-of-Bounds Read | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11903 | Medium | DHCP | Exposure of Sensitive Information | Treck TCP/IP 6.0.1.28 |
| CVE-2020-11904 | High | Memory Allocation | Out-of-Bounds Write | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11905 | Medium | DHCPv6 | Exposure of Sensitive Information | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11906 | Medium | Ethernet Link Layer | Integer Underflow | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11907 | Medium | TCP | Improper Handling | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11908 | Medium | DHCP | Exposure of Sensitive Information | Treck TCP/IP 4.7.1.27 |
| CVE-2020-11909 | Medium | IPv4 | Integer Underflow | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11910 | Medium | ICMPv4 | Out-of-Bounds Read | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11911 | Medium | ICMPv4 | Missing Authorization | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11912 | Medium | TCP | Out-of-Bounds Read | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11913 | Medium | IPv6 | Out-of-Bounds Read | Treck TCP/IP 6.0.1.66 |
| CVE-2020-11914 | Medium | ARP | Out-of-Bounds Read | Treck TCP/IP 6.0.1.66 |
The library is currently used by leading vendors like HP, Cisco, Baxter, B. Braun, Schneider Electric, Intel, and Rockwell Automation, and in multiple industries, such as medical, transportation, industrial control, enterprise, retail, and finance. The types of devices affected from this vulnerability range from everyday office devices like printers and access points to specialized devices like infusion pumps and industrial control devices. Since this library not only is used directly by the equipment vendor but also is integrated into various third-party software suites, tracking the presence of this library and patching it would be a challenge for consumers. Vendors have released advisories about specific devices that have been affected by Ripple20.
Risk Assessment
The risks that are associated with Ripple20 include:
- Attackers taking remote control of an internet-facing device, causing the device not to perform as expected or shutting down the device entirely.
- Once attackers have infiltrated a device, they can exploit other vulnerabilities in the library and spread the attack to devices in the same network segment.
- An attacker can also gain control over all the devices in a network segment by gaining access to a compromised device in the internal network (like a router).
- Sophisticated attacks, like MITM and DNS Cache poisoning, can be potentially performed by the attacker from outside the network boundaries.
Customers should ensure their IoT devices do not have any unused ports open, which will limit the entry points available to an attacker. Sensitive devices should maintain proper network segmentation by not being in the same network as guest devices or devices that have ports open from the internet. Proper network segmentation greatly reduces the attack surface and prevents a vulnerable device from spreading the threat to a larger pool of devices. Social distancing applies to devices too!
All of these vulnerabilities are addressed in Treck’s TCP/IP library 6.0.1.66 and later. Specific vendors have also been releasing patches with the updated library to ensure the devices are no longer vulnerable. Here’s what a customer should do to ensure the devices no longer have the vulnerable library:
- Check the device inventory to find all possible vendors and devices in the network.
- Reach out to each individual vendor to determine if the device is vulnerable.
- Update to the latest firmware patches for all devices (specially for affected vendors). Irrespective of Ripple20, it is best practice to have up-to-date firmware installed.
Detection and Remediation
Palo Alto Networks IoT Security service can help pinpoint devices in your inventory that are vulnerable to the above CVEs. Powered by machine learning, our platform will determine the identity of devices down to the type, profile, and model. Vulnerabilities will be discovered based on these identities and displayed within the platform.
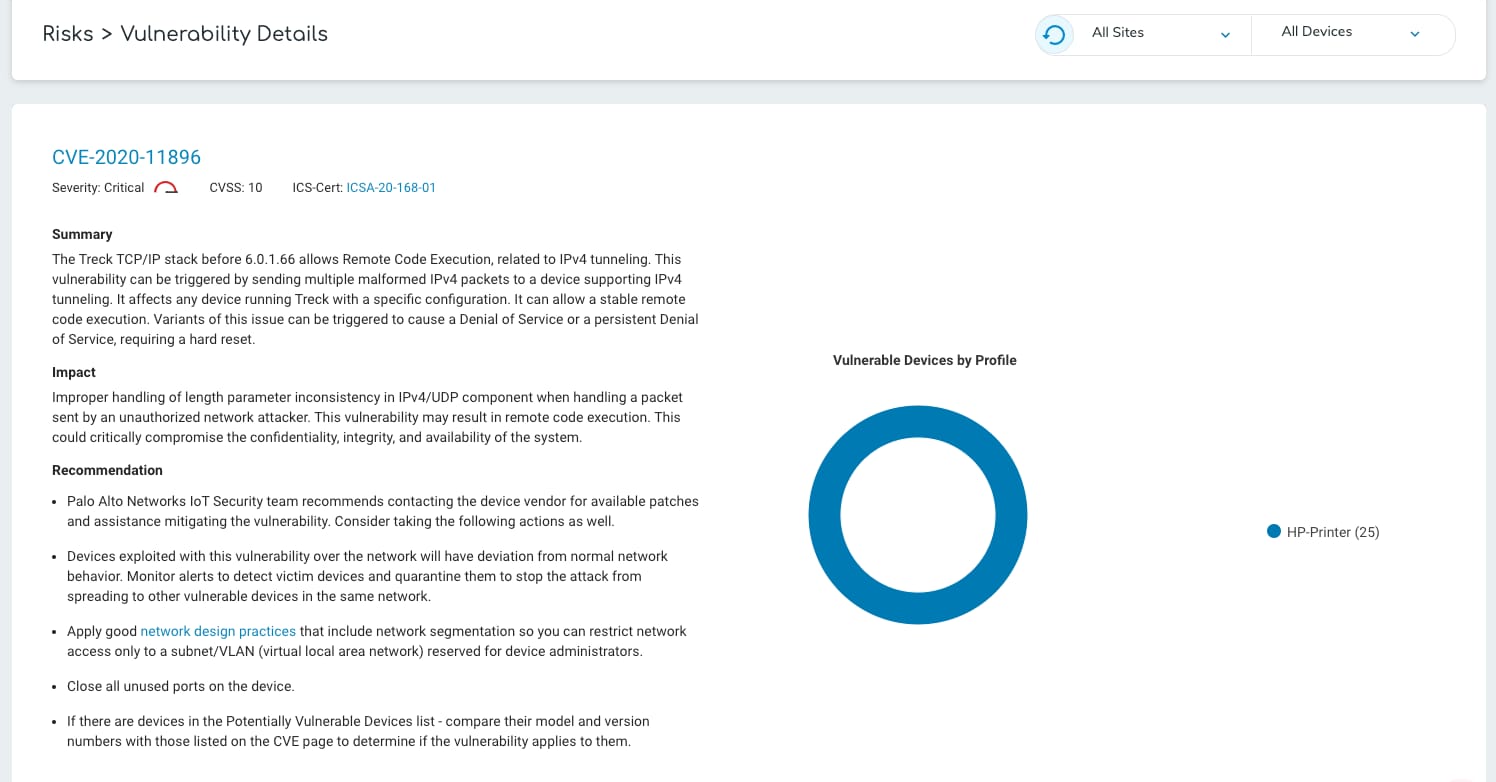
As various vendors release advisories related to devices affected in their product line, we are monitoring them and adding detections based thereon. Evaluate the impact of the vulnerability by logging in to your IoT Security service, navigating to the vulnerabilities page, and checking if any devices are vulnerable to Ripple20.
Palo Alto Networks IoT Security has additional detections in place in case any devices face any further security threats:
- When devices with these vulnerabilities are exploited, they will deviate from their normal network behavior. Our patented ML-based anomaly detection will generate alerts based on abnormal behavior (e.g., traffic from new sources, excessive connections, international connections). Victim devices can then be quarantined based on this behavior to stop attacks from spreading to other vulnerable devices in the same network.
- Check the devices that the Palo Alto Networks IoT Security service has listed as having confirmed or potential vulnerabilities from the list of the 19 above CVEs. These devices should be patched with Treck TCP/IP 6.0.1.66 (released on 30 March 2020) or higher.
- Different vendors and manufacturers that use the Treck libraries are currently researching and releasing firmware that addresses the issues exposed by Ripple20. Please check the respective vendor websites for the updated firmware versions. These firmware releases can also be used to patch your devices.
- If you are unable to update your devices, you should take the following steps to minimize risk and keep your network safe:
-
- Configure IoT and critical devices to ensure that they are not accessible from the internet.
- Properly configure your network segments to ensure IoT devices are behind firewalls, isolated from guest and business networks.
- Block any IoT traffic that has anomalous behavior.
For more information on Palo Alto Networks IoT Security, visit our website.
Aveek Das is a Senior Researcher in Threat Prevention. Derick Liang is a Data Scientist for IoT Security. At Palo Alto Networks, their work focuses on the security and analytics for the IoT Security Platform, mainly machine learning based threat and risk detection for IoT.