This post is also available in: 日本語 (Japanese)
The April 2021 Release for Prisma Cloud Propels Container Security Forward and Extends Our Workload Security Vision.
The April 2021 release for Prisma Cloud propels container security forward and extends our workload security vision. New functionality increases automation and detection, simplifies compliance checks and deepens visibility into malware threats for containers and hosts. Additionally, we are unveiling the industry’s first cloud native attack dashboard that extends the MITRE ATT&CK® framework.
The Prisma Cloud team wants to help ensure no workload is left unprotected, and our latest release brings us closer to that goal. Enterprises increasingly rely on diverse cloud native application portfolios as they select the cloud platform best suited to a given goal or strategy – simultaneously leveraging hosts, containers and serverless architectures for workloads. According to the 2020 State of Cloud Native Security Report, enterprises expect to run as much as 64% of their workloads in the cloud by 2022, spread nearly equally across VMs (30%), containers (24%), managed container services (21%) and serverless (22%).
But because the precise composition of these portfolios can vary widely across teams and projects, holistic security will require comprehensive security platforms that can overlay centralized controls and visibility, as Gartner notes in its Market Guide for Cloud Workload Protection Platforms (CWPP).
In support of this need, we are excited to announce the latest release for Cloud Workload Protection in Prisma Cloud, which includes:
- Automated detection and protection of cloud VMs.
- The industry’s first cloud native-focused Attack framework.
- Enhanced malware analysis for hosts and containers with WildFire integration.
- An improved compliance dashboard for analyzing security posture against leading frameworks.
- Virtual patching in the Web Application and API Security module.
- Git repository scanning using the twistcli tool.
- And more.
Let's explore some of the details of these new capabilities.
Host Security: Auto-Detect and Auto-Protect Cloud VMs
Virtual machines that run in public clouds require purpose-built security to streamline protections at scale; as an organization’s cloud footprint increases, it becomes harder to track and protect the growing number of VMs.
To mitigate these issues, Prisma Cloud now automatically detects unprotected VMs running on Amazon Web Services (AWS), Microsoft Azure and Google Cloud.
To then seamlessly deliver protection, Prisma Cloud can automatically deploy our Defender agent on those VMs, giving security teams assurance that the workloads are protected against anomalous behavior and active threats.
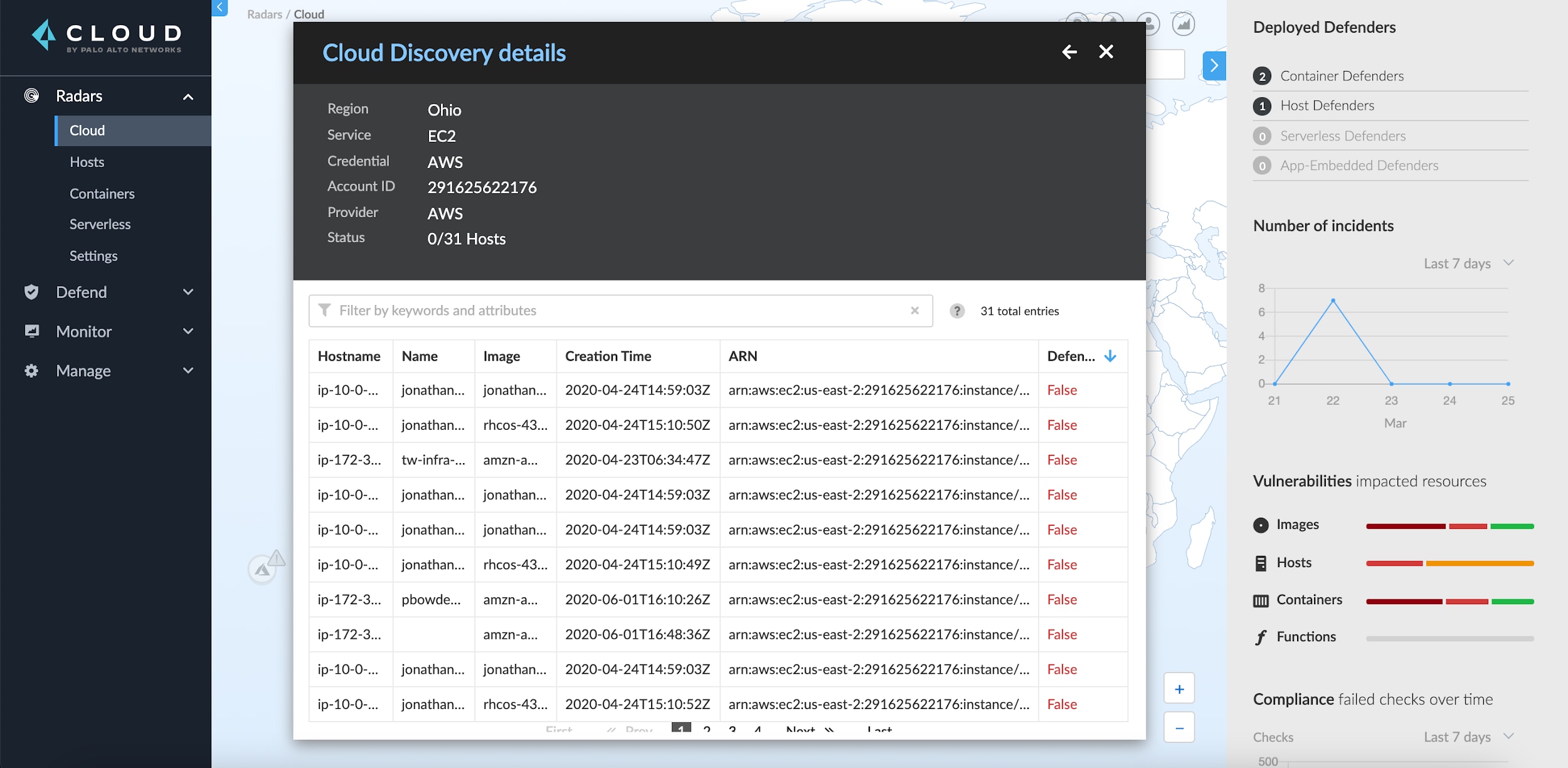
At launch, customers can enable auto-deployment for Amazon Elastic Compute Cloud (Amazon EC2) instances, with support for Azure and Google Cloud coming soon.
The Industry’s First Comprehensive Attack Framework for Cloud Native Apps
Prisma Cloud delivers comprehensive workload protection with runtime defense – automatically modeling baseline application behavior, then generating alerts for any deviation from normal activity or emerging threats. Similarly, organizations often use third-party frameworks, like the MITRE ATT&CK Framework, to measure the effectiveness of their security procedures and to identify areas of improvement.
In this latest release, Prisma Cloud offers a new interactive dashboard that correlates an attack framework to 12 distinct categories of security audits and events. This dashboard is the first of its kind – purpose-built for cloud native applications. It provides a consolidated view of an organization's entire cloud native app portfolio, whether running on cloud VMs, containers or serverless architectures.
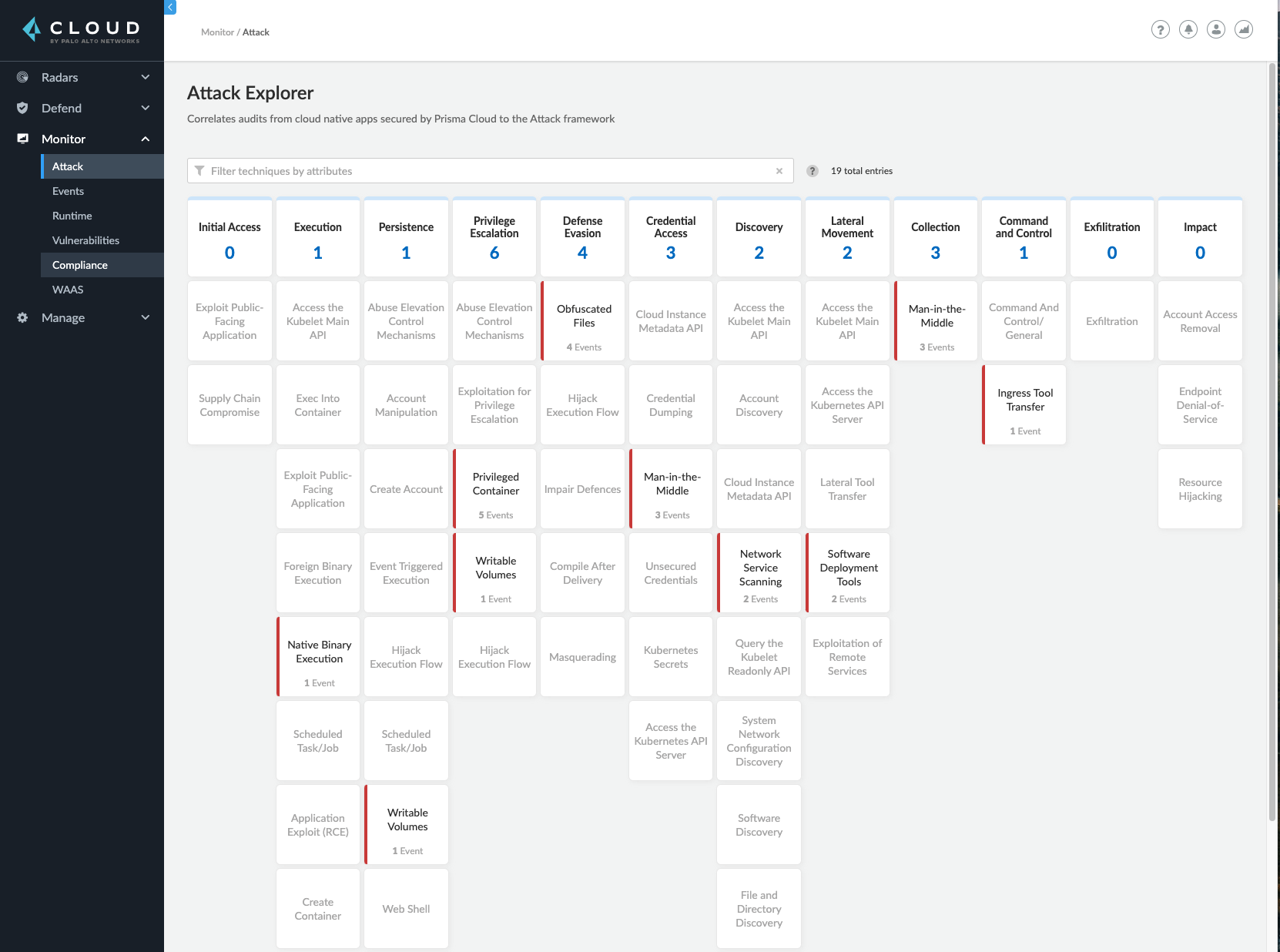
Customers can easily track trends over a period of time and evaluate how their defense capabilities map to specific threat scenarios, better enabling potential incident response and remediation.
Anti-Malware Capabilities and WildFire Integration Add Full-Lifecycle Malware Analysis for Hosts and Containers
Prisma Cloud delivers vulnerability intelligence, advanced threat protection data and malware feeds via the Prisma Cloud Intelligence Stream. Customers get accurate, precise risk prioritization and threat prevention, even in isolated environments.
To bolster this intelligence, Prisma Cloud now uses Palo Alto Networks WildFire intelligence to scan unknown binaries both at runtime and in CI/CD scenarios.
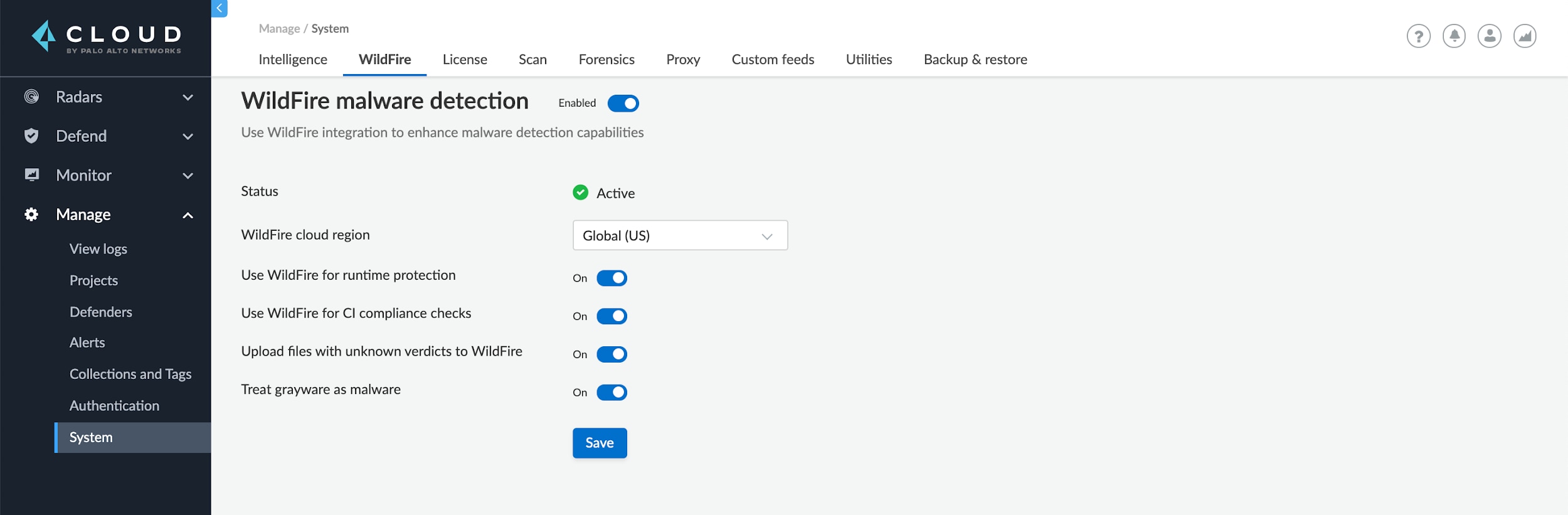
Once customers set up a simple policy, all unknown binaries will be sent to the WildFire engine, which runs the binaries in an isolated sandbox and determines their risk level. This gives teams an additional layer of runtime protection and deeper visibility into malware threats during CI/CD processes. Additionally, new anti-malware and exploit prevention capabilities cover hosts and containers.
Simplified Compliance for Hosts, Containers and Serverless Apps
DevOps, security and compliance teams frequently need to meet internal compliance requirements while also achieving standards for external frameworks such as PCI-DSS, HIPAA, and GDPR.
To assist in meeting these requirements, this release includes an improved Compliance Explorer UI that makes it easier to analyze your security posture against leading compliance frameworks and CIS Benchmarks.
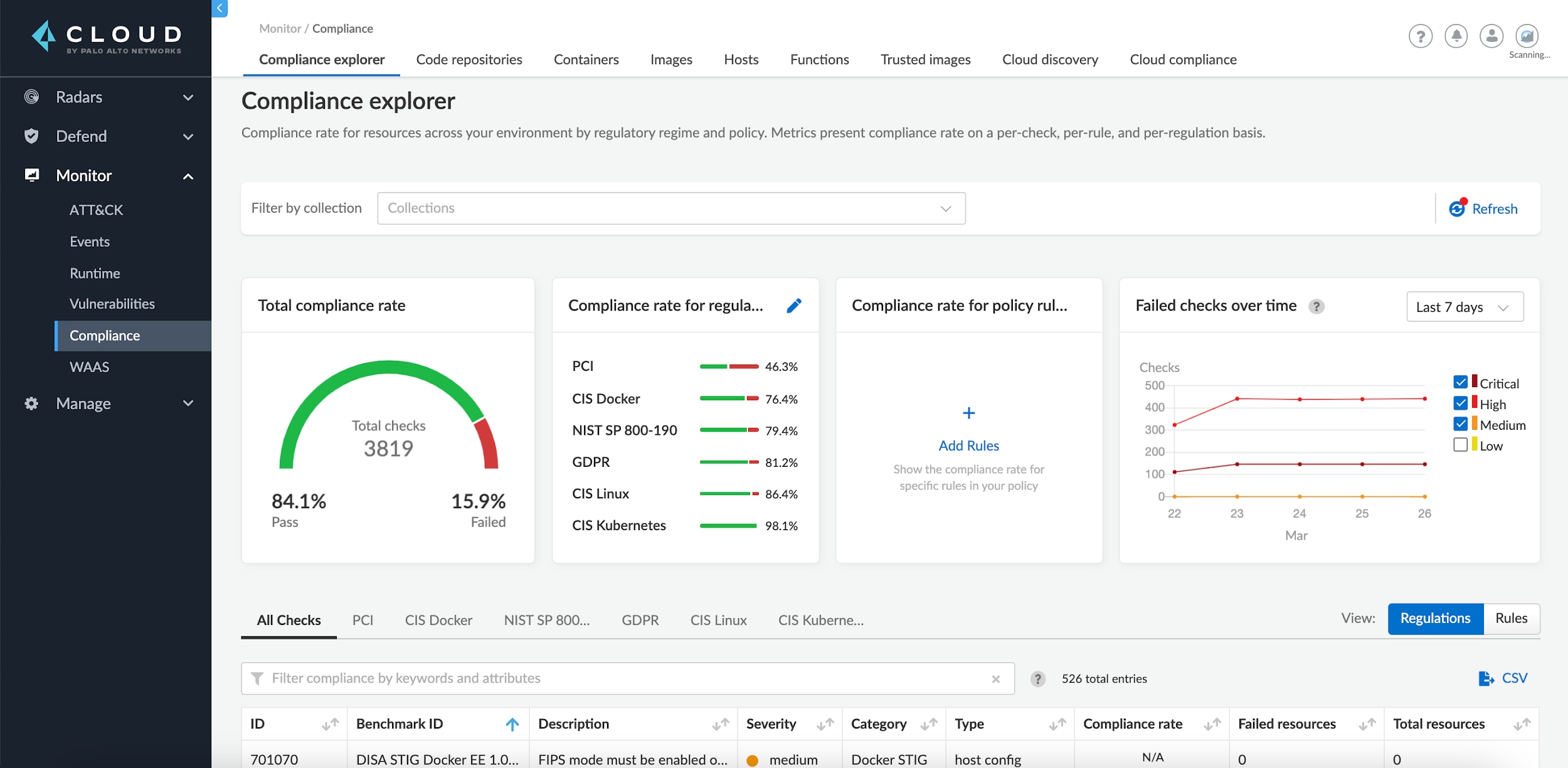
This release also delivers the industry’s first compliance solution for implementing the Docker Enterprise Defense Information Systems Agency (DISA) Security Technical Implementation Guide (STIG). This framework provides coverage for host configurations, containers and images, and orchestrator configuration. Importantly, the STIG leverages previous National Institute of Standards and Technology (NIST) Special Publications, including NIST SP 800-53 and NIST SP 800-190, the latter of which was co-authored by John Morello, Prisma Cloud vice president, product, while he was CTO at Twistlock.
Web App and API Security: Virtual Patching
Security teams must quickly react to new threats and enable protection across their cloud native infrastructure. To address these challenges, the Web Application and API Security (WAAS) module now supports dynamic policy creation, also known as virtual patching, to more quickly enable protection wherever WAAS is active.
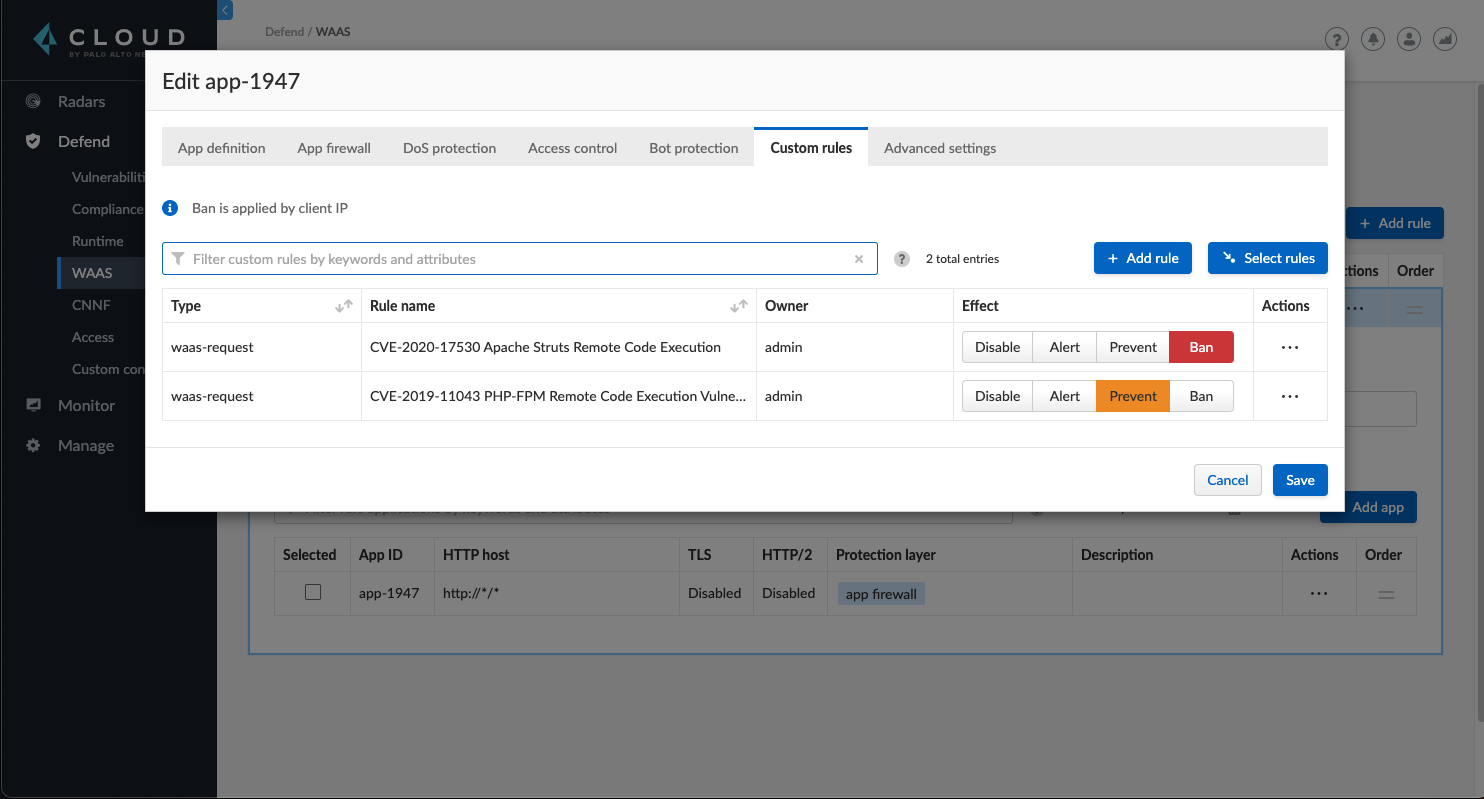
Dynamic policies created by Prisma Cloud Labs, our own threat research and R&D team, are distributed via the Prisma Cloud Intelligence Stream to ensure more comprehensive coverage across new and emerging attack vectors. Policies are distributed automatically based on deep knowledge of CVEs across end-user environments.
Shift Left: Wider Git Repo Availability and Enhanced License Detection
We previously added capabilities for identifying vulnerabilities in git repositories to help developers and DevOps teams address flaws earlier in the software development lifecycle.
This latest release now lets users scan code repositories using the twistcli command line interface, and includes new support for scanning GitHub Enterprise repositories. This offers developers even more flexibility for scanning git repos.
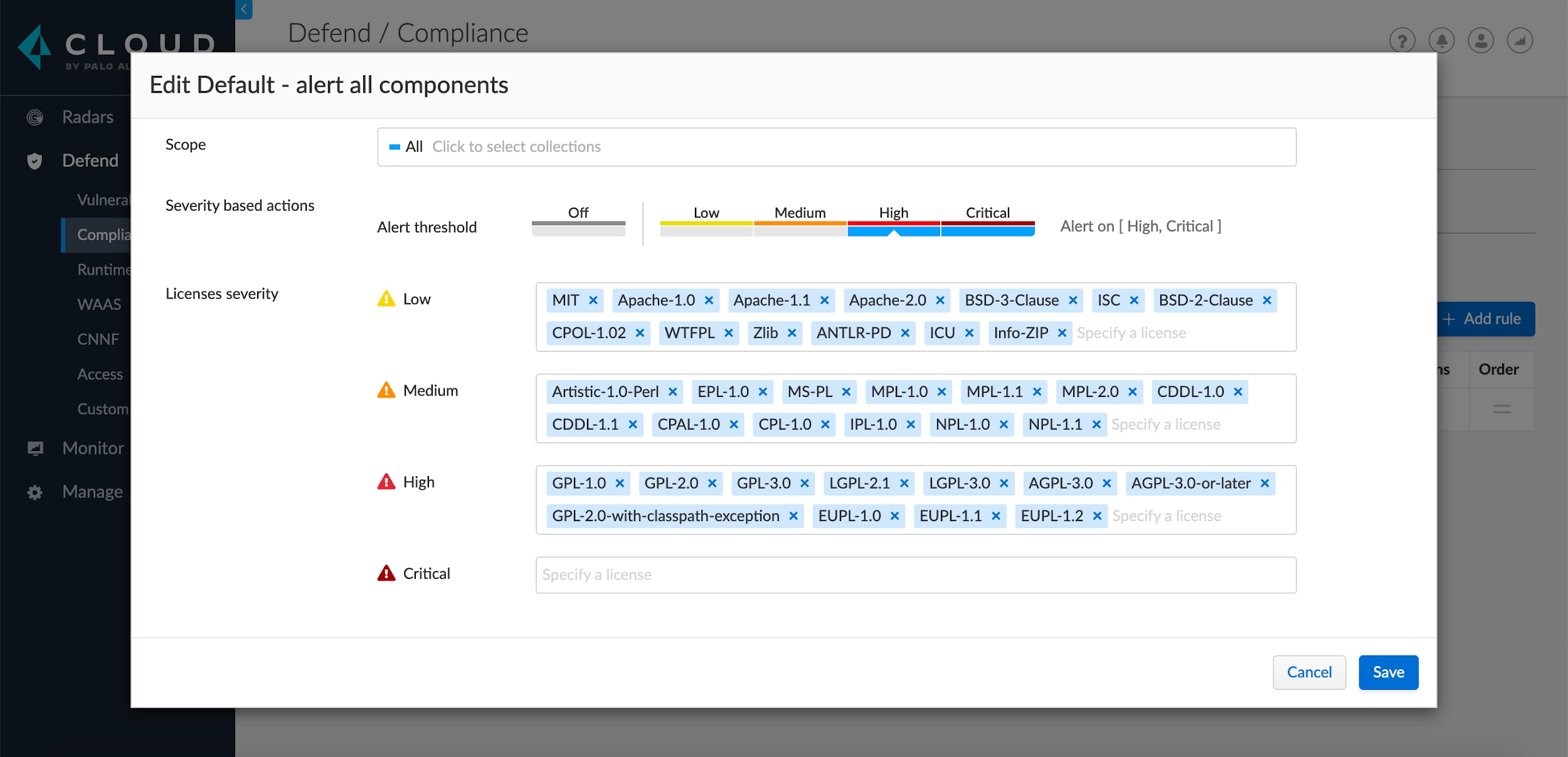
Additionally, we've added advanced license detection to help identify open source licenses in packages, as well as license compliance rules that are set in Prisma Cloud to monitor and manage usage within an organization. At launch, supported license categories include MIT, LGPL and GPL, along with 20 others.
Additional Capabilities in Prisma Cloud
In addition to these extensive capabilities, the April 2021 release for Prisma Cloud also delivers:
- Deeper support for AWS Fargate: Users can now run the Prisma Cloud Compute Edition Console on AWS Fargate, and get Fargate-specific vulnerability and compliance views.
- Enhanced Role-Based Access Control (RBAC): Prisma Cloud now includes customized role creation, with Assigned Collections available in Prisma Cloud Enterprise Edition for the first time. This provides DevOps and security teams more granular control over the configuration of dashboard views based on user roles.
Next Steps for Managing Your Cloud Native Applications
You can learn more about securing diverse architectures into runtime with our latest ebook, Why and How to Add Runtime Defense to Your Cloud Security Strategy.
And for a deeper look at the cloud native Attack Framework within Prisma Cloud, join our discussion on May 25, 2021, Cloud Native Matrix to Protect Hosts, Containers & Serverless. Led by our own product managers, we'll examine real use cases from customers while providing a demonstration of the interactive dashboard.