This post is also available in: 简体中文 (Chinese (Simplified)) 繁體中文 (Chinese (Traditional)) 日本語 (Japanese) 한국어 (Korean)
There is no debate that the majority of applications have moved to the cloud, creating a demand for cloud-native security. In fact, Gartner estimates that by 2025 over 95% of new cloud workloads will be deployed on cloud-native platforms, which is up from 30% in 2021.
With the move to deliver applications through a cloud infrastructure (or for most of us, a hybrid and multicloud infrastructure) comes a host of risks in every stage of the application lifecycle.
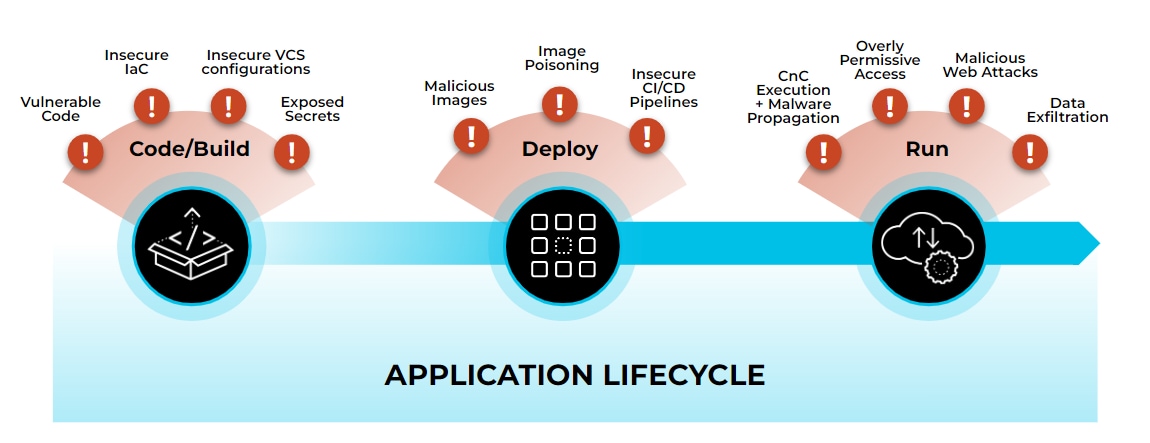
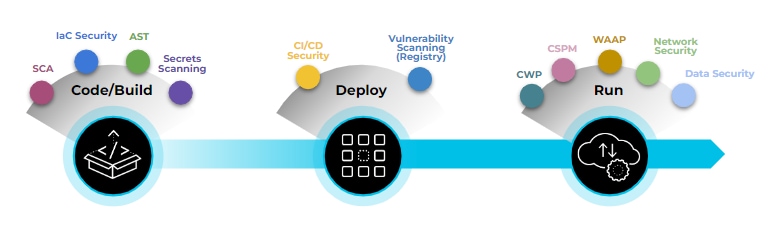
Most organizations have responded to the risks of cloud-based application delivery by adopting a specific security tool to address each risk throughout the application lifecycle of code, build, deploy, run. Organizations had to consider an alphabet soup of point products that target specific use cases. A few of these products include IaC (Infrastructure as Code) security, SCA (Software Composition Analysis), CSPM (Cloud Security Posture Management), CWP (Cloud Workload Protection), WAAP (Web API & Application Protection), and the list goes on. This has resulted in 10-15 cloud security point products cobbled together for many organizations.
CISOs struggle to staff and train their teams as they take on more tools. Furthermore, because a hodgepodge of tools provide fragmented views of risk, security teams are left with no context throughout the application lifecycle. In the world of modern application development and cloud migration, point tools are expensive to manage, don’t offer continuous or real-time protection, and often lack the ability to deliver a prevention-first strategy.
Cloud-Native Application Protection Platforms (CNAPP) are meant to address these challenges.
Code-to-Cloud CNAPP
At Palo Alto Networks, we listen intensely to our customers, external security experts and our internal security analysts for roadmap guidance. It isn’t enough to keep ahead of cloud security threats. We have to also offer a product that is easily operationalized by developers, cloud IT and security teams, even across the most complex virtual machine, container and serverless environments. From this input, we defined our five foundational principles required in building a code-to-cloud CNAPP. And, we hope other vendors will follow because friction between developers and security teams is slowing digital transformation and feeding the hacker community.
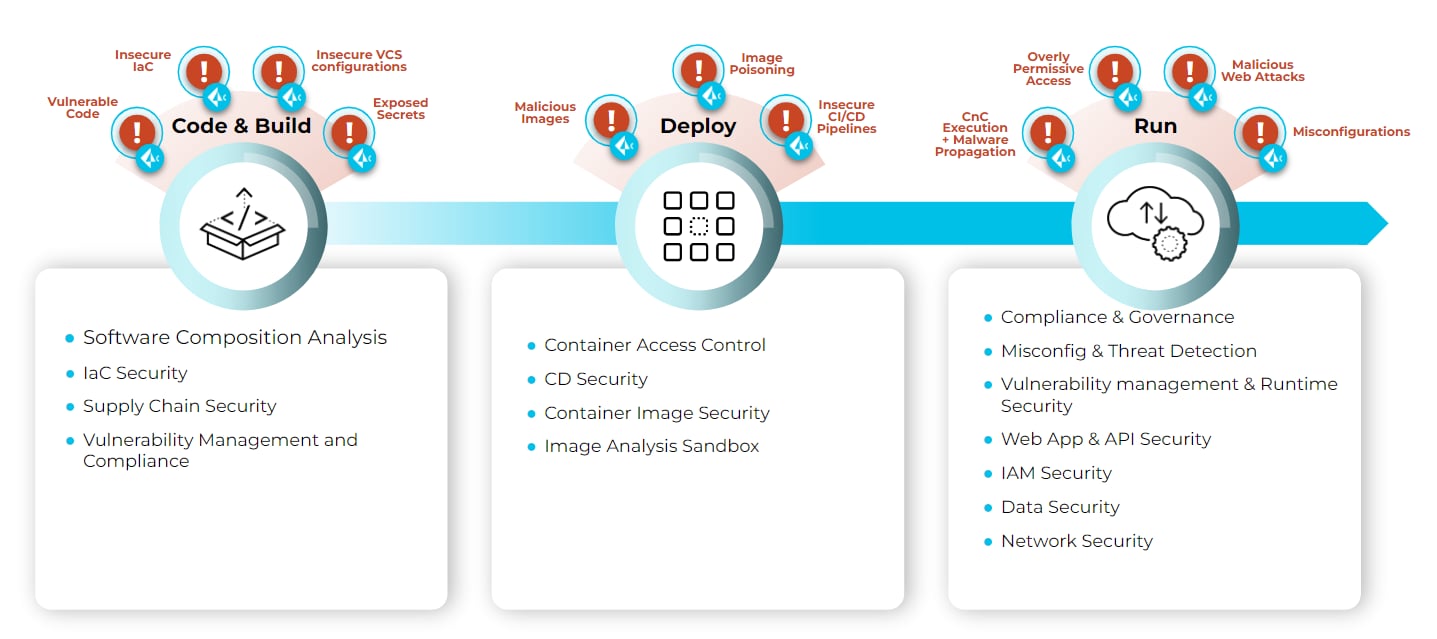
- Comprehensive Security from Code to Cloud: Code-to-cloud CNAPPs must support the full application lifecycle security, offering visibility and protection across Code, Build, Deploy and Run.
- Continuous, Real-Time Visibility: Code-to-cloud CNAPPs must continuously monitor cloud network activities and user behaviors, employing Machine Learning (ML) to identify what’s normal, and then alerting to behaviors that deviate from the baseline. Detecting misconfigurations, vulnerabilities and threats has to occur in minutes. Scanning once a day or even waiting hours between scans gives hackers too much time in your environment.
- Prevention-First Protection: Visibility alone isn’t security. Code-to-cloud CNAPPs must provide automated and real-time prevention capabilities for blocking exploits, as well as remediating vulnerabilities and misconfigurations across the application lifecycle. Layers of defense are required at each application lifecycle phase to remediate risks before they can be exploited.
- Choice for Every Cloud Journey: Code-to-cloud CNAPPs must support your current security needs, regardless of where you are in your cloud journey, and be able to extend support to wherever your personal cloud migration journey takes you. A code-to-cloud CNAPP allows you to change or add cloud service providers, workload architectures, CI/CD pipelines, IDEs and repositories without also having to onboard another vendor, deploy and learn an entirely new product.
- Cloud Scale Security: Code-to-cloud CNAPPs must be a scalable, comprehensive approach to cloud security that ensures coverage of threats across the full lifecycle of the application. Security must scale automatically to match the cloud infrastructure across hybrid and multicloud environments while protecting infrastructure, code, applications, APIs, data and identity.
Prisma Cloud, the Industry’s Only Code-to-Cloud CNAPP
Prisma Cloud secures applications from code to cloud and across multicloud environments. The platform delivers continuous visibility and threat prevention throughout the application lifecycle, including zero day threats. The platform’s code-to-cloud coverage includes optional components that can be added as required for securing code, infrastructure, workloads, data, networks, cloud identities, web applications and APIs across your cloud-native environments. Prisma Cloud is the most comprehensive platform that addresses security needs at every step in the cloud journey.
New CNAPP Capabilities in Prisma Cloud 4.0
Prisma Cloud customers benefit from constant CNAPP innovation. The Palo Alto Networks investment in Prisma Cloud keeps the platform on the cutting edge of security capabilities, addresses new threats, improves operationalization, and extends environment support. Here are just a few of the new capabilities we recently announced:
- Software Composition Analysis (SCA): Proactively address open source vulnerabilities and license compliance issues with developer integrations and infrastructure-awareness prioritization. Prisma Cloud uniquely combines its Infrastructure as Code analysis to provide additional context and SCA findings to identify vulnerabilities embedded in container dependencies while also offering insightful remediation recommendations. You can learn more about our innovative approach in the SCA launch blog.
- Software Bill of Materials (SBOM): Maintain a complete codebase inventory (including open source license and version information) of every application component used across clouds.
- Data Security for Azure Storage Blob: Extend Palo Alto Networks Enterprise DLP & WildFire malware scanning solutions to Azure Blob Storage for data classification and malware detection as part of Prisma Cloud.
- Expanded Visibility Across Azure Environments: Rapidly provide CSPM visibility as Microsoft Azure introduces new services.
- True Internet Exposure for Azure: Analyze all network pathways on Azure and identify internet exposed assets, in addition to AWS.
- Command Center: A dashboard for at-a-glance determination of highest priority risks and incidents across cloud assets to help prioritize remediation.
- Unified Cloud Inventory: Unify misconfiguration and vulnerability data from across the platform to deliver contextual risk for your cloud assets.
- Granular RBAC: Granular and consistent management of least-privilege access to Prisma Cloud features for different user profiles.
- Japan Hosting: Further expand Prisma Cloud performance and scale in Asia with the addition of a Japan hosting site.
Trusted, Proven and Award Winning

Today, Prisma Cloud is trusted by over 1900 customers globally, securing over 1.5 billion assets and protecting over 2.5 million workloads by processing over 2 billion events every day. Additionally, Prisma Cloud platform is continually recognized across the industry, and most recently by SC Magazine for Best Cloud Workload Protection Solution. Idan Tendler, vice president of Code Security, was honored as Innovator of the Year. That’s right, we were recognized from code to cloud - Code Security innovation and best Cloud Workload Protection!
Join us on Oct. 20 for a LinkedIn Live event, where our product leadership will be discussing our vision for cloud security and how Prisma Cloud can secure your application modernization.