Better Together: Agentless Scanning and Agent-Based Protection for Comprehensive Cloud Security
Many in the security industry have been pondering recently whether “agentless” or “agents” are most effective. The answer is simple: use both for comprehensive security.
Cloud native workloads are all about flexible deployments and agnostic approaches that don’t tie you in with a specific provider, vendor, host OS or tool. Today’s applications are about mixed workloads, multi-cloud environments and different runtimes. So, why should security be any different? You shouldn't have to compromise on your security needs based on a security vendor’s architecture.
With that vision in mind, Prisma Cloud is proud to be the first security platform to offer both agent-based and agentless security together from a single solution, giving you and your teams the flexibility and choice to deploy or activate the right method of protection in a mixed environment.
Agentless and Agent-Based Protection Go Hand-in-Hand
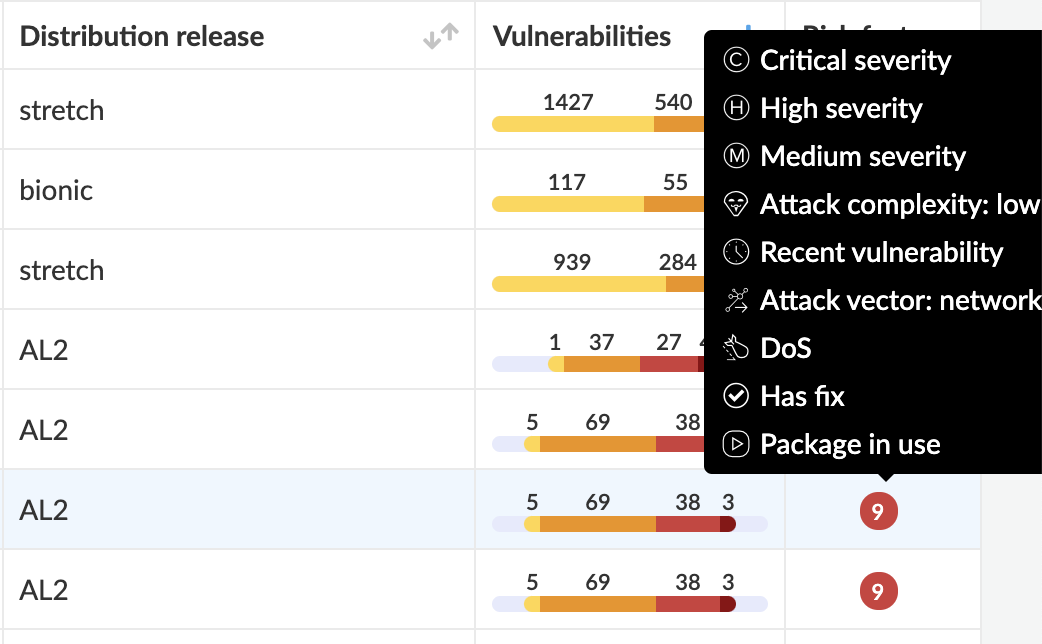
Agentless scanning helps users inspect the risks and vulnerabilities of a virtual machine without having to install an agent or affecting the execution of the instance. In a mixed environment, having just agents or just agentless scanning will not meet all of the diverse security needs. A combined approach is needed in order to ensure you have complete coverage.
For example, some workloads in your environment could be web server applications that require web application and API protection capabilities to alert and prevent attacks like DoS requests, SQL injection or cross site scripting from affecting your service. In order to continuously monitor requests and block such attacks from affecting your application workloads, you need agents.
Whereas if you have managed clusters or environments where you don’t directly access host kernels or need blocking capabilities, agentless scanning provides deep insights leveraging cloud service provider API calls, providing visibility into unpatched vulnerabilities or exposed risks. Here’s how the nature of cloud native workloads drives the need for both of these features to go hand in hand.
Differing access levels across your environment
As a security team, you may not always have access to all hosts to deploy agents. For environments where you need visibility into risks and vulnerabilities of instances without having to install an agent or affecting the execution of the instance, enable agentless scanning. It’s quick to set up, easy to configure at a large scale and there is no need for SSH access into every host in order to deploy and update running agents.
This should be your foundational setup. As soon as you onboard accounts, set up agentless scans across all resources in your cloud accounts for vulnerability scans before active, preventive defense.
Diverse sensitivity levels
NIST Special Publication 800-190, the Container Security Guide, advises separating workloads by sensitivity level across your deployment. Imagine if you were a financial institution that requires strict enforcement of PCI compliance. As a best practice, you would separate your workloads by sensitivity depending on the purpose the applications serve. You wouldn’t want to run your web service containers that are exposed to the internet on the same host that has access to your S3 buckets storing sensitive information.
While you separate your cloud workloads by sensitivity, security should follow suit. Expanding on the scenario from above, if you have 10 cloud accounts with a total of 100 EC2 hosts, use agentless scanning as your baseline across the entire environment. Not all hosts within the cloud accounts would hold critical sensitivity. Some of those hosts could be used for testing or QA or development. It’s important to still scan all accounts for open risks and vulnerabilities to understand your overall security coverage and possible exploits.
Then, for your production hosts in sensitive environments, monitoring alone is not enough. You would want to prevent unauthorized access to your file directories that hold sensitive data, prevent malware from being downloaded, block connections to suspicious endpoints proactively, block images that fail PCI compliance standards from running in your production hosts. Thus, with a combined approach you leverage the right security for varying sensitivity.
Evolving workload types
We see workloads evolving into various abstraction layers - containers, serverless, app-embedded models, containers as a service offerings and so on. While some resources like hosts, clusters, serverless functions can be scanned by the cloud provider’s API calls, some require having an inline defense in place for runtime security. For example, when an application running in a serverless function or Fargate task is executed, use embedded agents to enforce network security to only allow connections to trusted domains while blocking connections to suspicious IPs sourced from threat feeds.
Prisma Cloud’s architecture agnostic approach
Given all factors above, Prisma Cloud provides a flexible architecture agnostic experience across the platform so you can focus on security policies important to you without worrying about the type of deployment.
Easily switch between agent-based and agentless
We understand that there are times when you feel the need to switch between agent-based to agentless protection or vice versa as your applications evolve. Prisma Cloud makes it easy to deploy and set up either method of scanning and also easy to switch between the two methods with no overhead to users. You can deploy agents on a host that is being scanned by Agentless scanning without worrying about disabling Agentless manually. Prisma Cloud will automatically disable Agentless scans, so your scans are not duplicated. And if you choose to switch back to agentless, simply uninstall the Defenders without reconfiguring the Agentless setup.
Single policy mechanism
One place for all! You don’t need to worry about managing policies separately based on architecture types. Set up policies by features instead of scan methods and let Prisma Cloud handle implementation.
Single licensing
Regardless of agentless or agent-based approaches, you will never be double charged for a resource. At a point of time, only one scan method will be active even on resources that have both agents and agentless scanning enabled. No manual user intervention is needed.
Same API calls and reporting UI
Across the entire platform, the reporting structure stays the same - contextual risks based on all scanned resources regardless of scanning method. You don’t have to worry about changing your API calls, reporting dashboards, or scan through separate UI tabs for each data. You will continue to have the same experience throughout the product.
Full Stack Security from Prisma Cloud
If you want a full stack cloud native security solution, you should think of adopting both technologies so there are no gaps in security coverage across your entire environment. Especially if you are in a hybrid cloud space with workloads in major cloud providers and private data centers, Prisma Cloud recognizes the need for flexibility and hence is the only platform to provide an end-to-end solution with both agent-based and agentless security.
Here’s how both architectures can be used together according to different security needs within your organization:
Use Agentless for
- Easy account-based setup with snapshot-based scanning
- Immediate visibility into risks and vulnerabilities in instances
- Broader security coverage across cloud accounts without needing access into each machine
- No agent deployment or maintenance required
While agentless is the first step in providing easy visibility into risks, critical production environments require runtime blocking or prevention for malicious activity.
Use Agents (Defenders) for
- Continuous monitoring of workloads at runtime
- In-depth forensic capabilities
- Blocking or preventing suspicious activity
- Web application firewall capabilities
To learn more about Agentless Security and our Prisma Cloud 3.0 launch, visit the Prisma Cloud website.
Related Blogs
Subscribe to Cloud Native Security Blogs!
By submitting this form, you agree to our Terms of Use and acknowledge our Privacy Statement. Please look for a confirmation email from us. If you don't receive it in the next 10 minutes, please check your spam folder.