Strengthening Integrations in our Cloud Native Security Platform
In our latest CWPP release of Prisma Cloud, we enhanced and expanded our best-of-breed capabilities and built upon our award winning technology to protect cloud workloads across security for hosts, containers, and serverless applications. All of our enhancements contribute to strengthening integrations in our Cloud Native Security Platform: Prisma Cloud.
At Prisma Cloud, we recognize that no one cloud service provider, or one cloud workload type is enough for all organizations. We acknowledged this early, introducing the industry’s first Cloud Native Security Platform which encompassed DevSecOps, CSPM, CWPP, CNS, and CIEM across workloads and cloud providers.
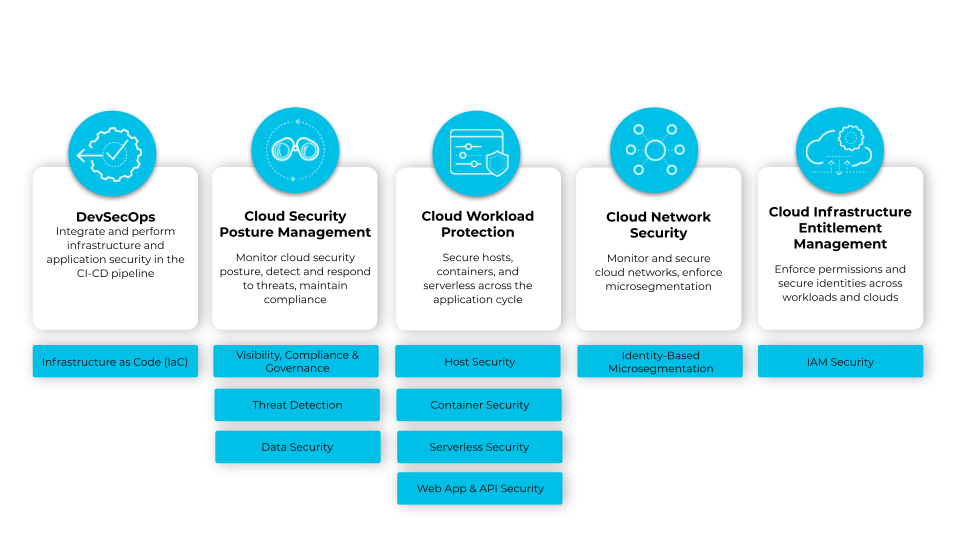
However, Cloud native security platform (CNSP), is more than just an umbrella for different products in a platform. A true CNSP solution is an integrated approach to securing an environment and applications, regardless of which modules they are using or how that might change in the future. It works across the software development life cycle (SDLC) and enables security to effectively shift left.
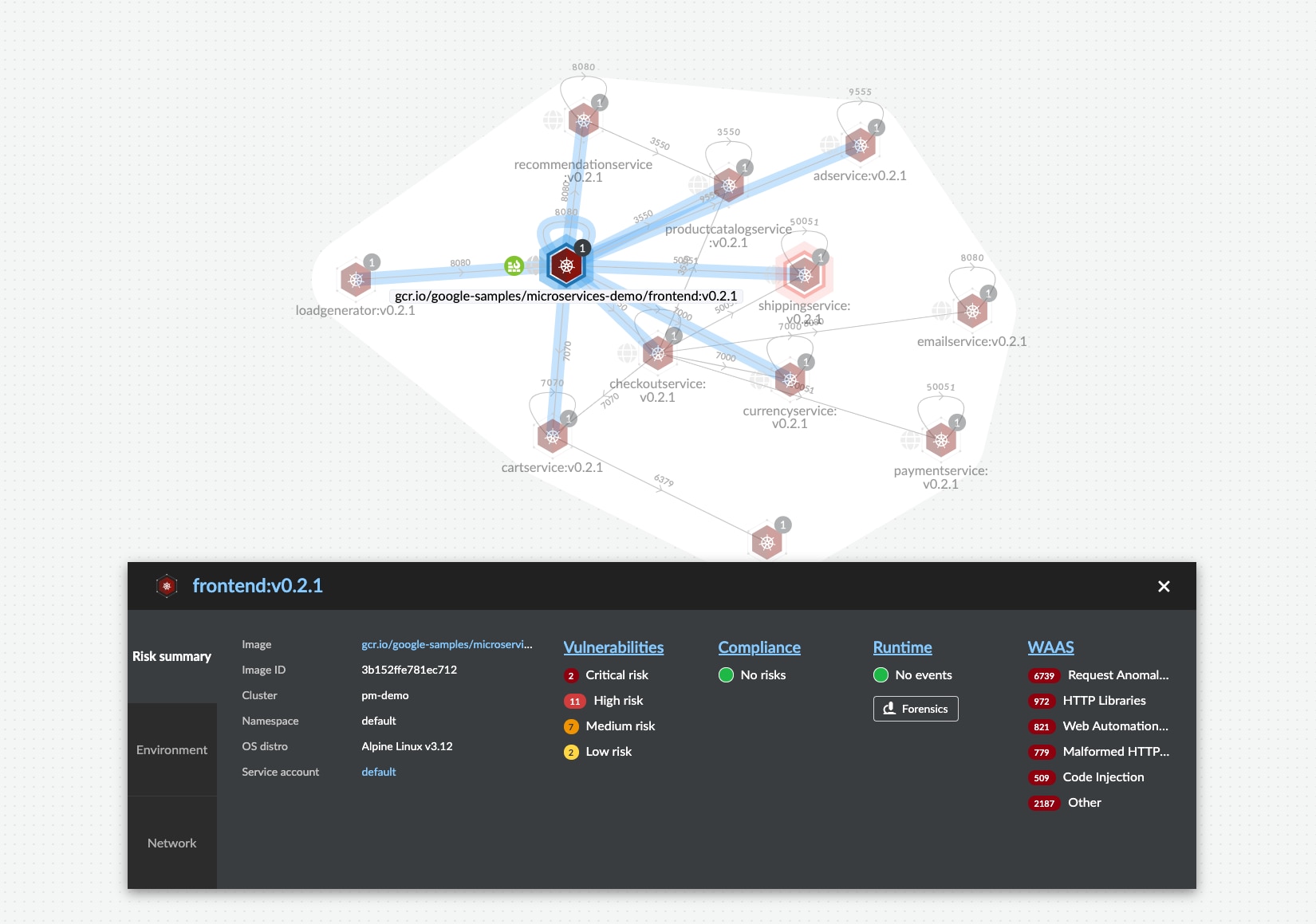
Let’s walk through an example that generalizes a real-world scenario. Say you own the operations of serving a bank’s website and you are hosting your web server in a Kubernetes cluster through containers. The application talks to an internal database connecting to S3 bucket for sensitive data storage.
In this case, consider the different attack surfaces -
- Web application prone to layer 7 attacks like SQLi, XSS scripting, etc. (WAAS)
- Container and image risks and vulnerabilities (Container security)
- Open ports or unmonitored access to Internet (Network Exposure)
- Cluster posture risks / misconfigurations leading to exposure (IaC and CSPM security)
- Underlying host misconfiguration and vulnerabilities (on Kubernetes nodes) (Host security)
- Poor posture management of data as part of s3 buckets (Data Security)
- Unmanaged Identity and access to sensitive data (IAM Security)
In this blog, I’d like to highlight from a Product Manager’s perspective, the integration strategy between CWPP and CSPM, through some of our recent updates along with new features. Working with customers, we realized that to create an efficient CNAPP platform, it is important to address three main integration categories for active users of the platform:
-
- Ease of Onboarding
- Ease of Configuration
- Ease of Reporting
Ease of Onboarding
The first step to securing cloud services and workloads should be a unified experience.
This new feature highlights the benefit of a CNSP: the ability for one part of the solution to alert and inform another.
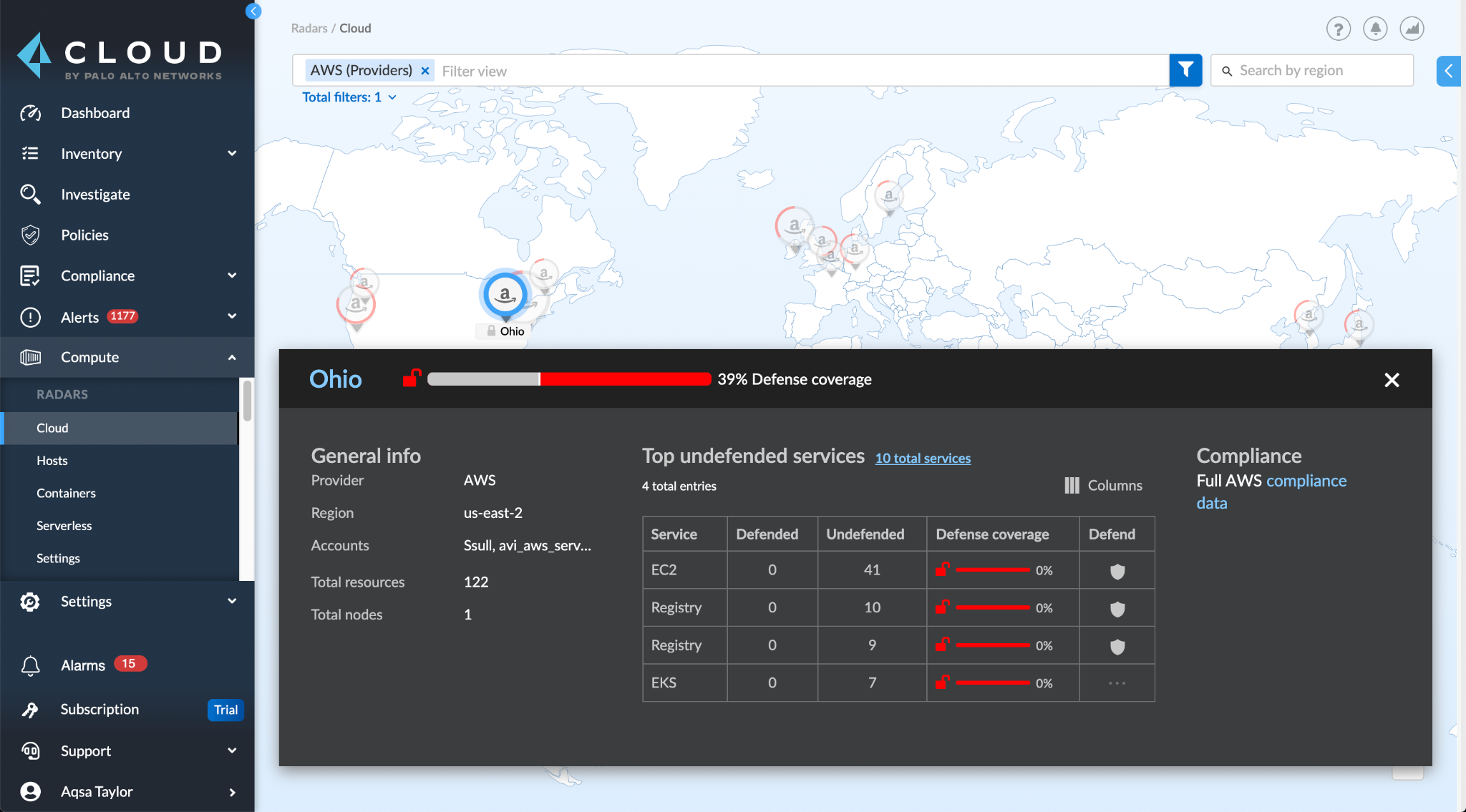
Once a cloud account is onboarded into the platform, CSPM will immediately analyze the security posture and state of cloud resources deployed in this account. At the same time, it is also available automatically for the CWP to discover unprotected workloads across the environment and, if the customer chooses, automatically deploy a Defender. Immediately the organization has the full range of CNAPP functionality at its disposal. No need to onboard in one part of a product and then another.
Not only does this integration ease workload discovery, but in this release, by re-using the same ingested metadata from cloud providers for both CSPM and CWPP, the time to scan for unprotected resources is reduced substantially, providing instant visibility into undefended workloads in your organization. Learn more about our cloud discovery feature here.
Accounts to Credentials
Prisma Cloud automatically translates onboarded cloud accounts in the platform used for CSPM and CWPP functionality into credentials that can be used for workload scanning features such as serverless function scanning, automatic runtime protection and registry scanning.
Ease of Configuration
As a platform, Prisma Cloud simplifies configuration while also taking into account the different personas and distributed teams involved in the remediation of alerts coming from CSPM and CWPP.
Granular Role Based Access Control
Prisma Cloud’s RBAC model provides the ability to segment data coming from different sources while also providing restrictive access into different views based on attributes such as image tags, namespaces, labels, etc. via Resource Lists. The segmentation is useful when you have large workload deployments with multiple teams working on multiple apps all in the same environment. For example, you might have a Kubernetes cluster that runs a shopping app, a travel app, and an expenses app. Different teams might be responsible for the development and operation of each app. An internal tools team might be responsible for the travel and expenses app, while a product team runs the shopping app.
Selecting a resource list reduces the scope displayed in Console to just the relevant resources. For example, the developer for the travel app only cares about vulnerabilities in the images that make up the travel app. All other vulnerabilities are just noise. Collections help focus the data.
Ease of Reporting
When alerting on security audits, providing flexibility in addition to central control addresses needs for both distributed and centralized teams.
Unified Notifications
With this new feature, you can configure your alert providers, whether it is Email, ServiceNow, JIRA, Slack or any provider from our supported list in one central place and regardless of the workload (VMs, containers, serverless functions) your notifications will be forwarded to the same channel. If you have multiple cloud service providers or even if you change in the future, your notifications are configured in a single location.
Remember that we are now operating across the software development lifecycle and DevOps teams. This same, single, notification configuration means that regardless of the automation that teams are using the notifications are delivered consistently and configured centrally.
With this new feature, not only can you target all the areas of risks listed above from a single security platform but also direct alerts from all those areas to a centralized notifications channel, so your incident response teams have full visibility and control over all workload layers that make up your application.
Set up Splunk configuration for CSPM alerts in platform, use the same configuration inside Compute to send container runtime audits as shown below
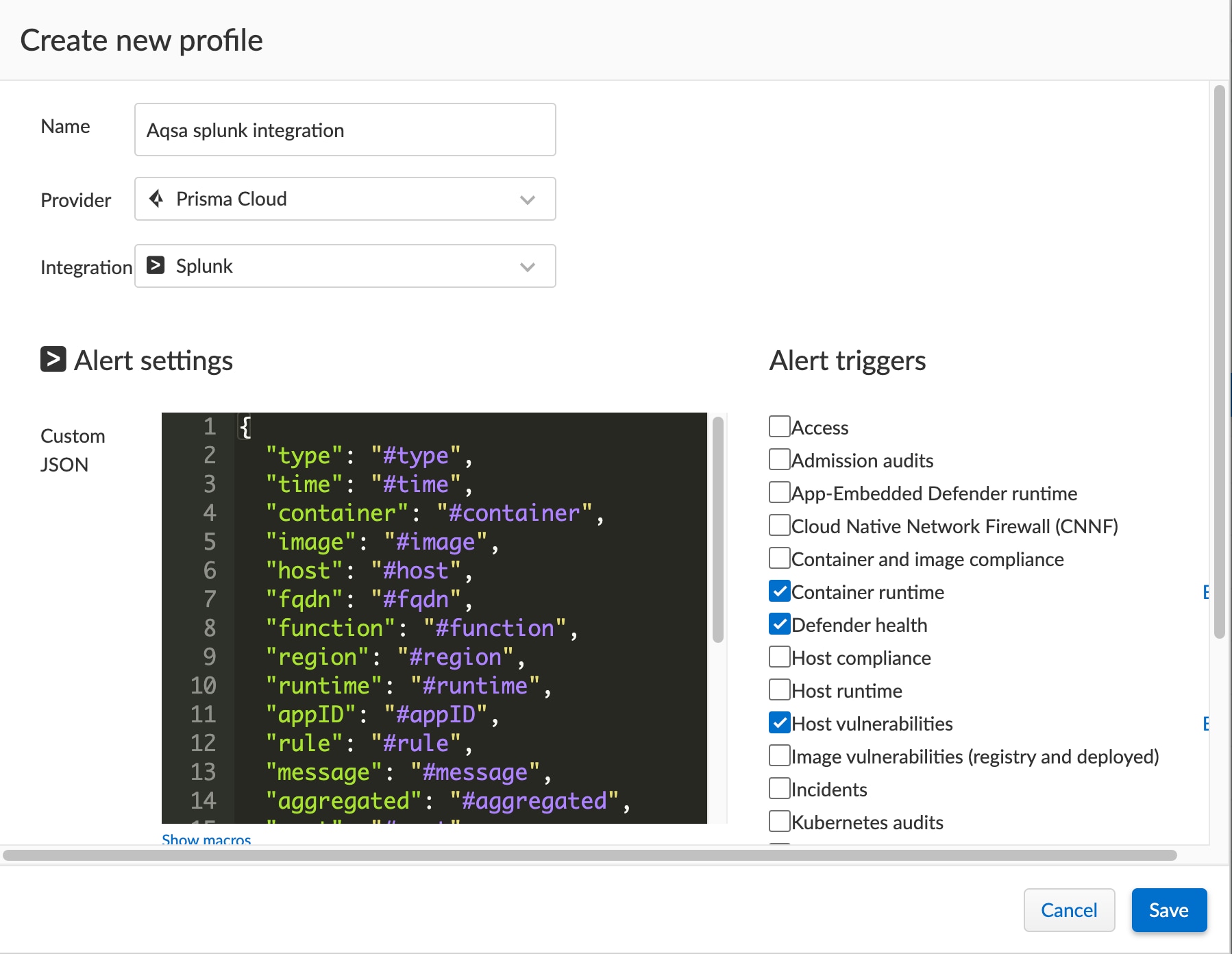
Check out more details on how to set up unified integrations here.
Get Started with Prisma Cloud
At Prisma Cloud by Palo Alto Networks, we’ve invested heavily in providing a solution that secures your diverse workloads across your private and public cloud environments across your SDLC, and most importantly across your changing business needs. All in a single comprehensive security platform.
Request a 30-day trial and learn how Prisma Cloud provides complete cloud native application protection in a single, unified platform.
Related Blogs
Subscribe to Cloud Native Security Blogs!
By submitting this form, you agree to our Terms of Use and acknowledge our Privacy Statement. Please look for a confirmation email from us. If you don't receive it in the next 10 minutes, please check your spam folder.